Search for topics
Trending Searches
Featured Articles

AI-Powered Deepfakes Used by North Korea’s UNC1069 to Infiltrate Crypto Companies
February 12, 2026
North Korea’s cyber operations are back in focus after new research exposed a group called UNC1...
Read More >
How Samsung Knox Strengthens Mobile Security and Helps Organizations Prevent Network Breaches
February 06, 2026
Network security breaches are becoming a serious concern for businesses across the world. Attacke...
Read More >
Uncovering a Long-Running Global Cyber-Espionage Campaign
February 06, 2026
A previously undocumented, Asia-linked cyber-espionage group has breached at least 70 government ...
Read More >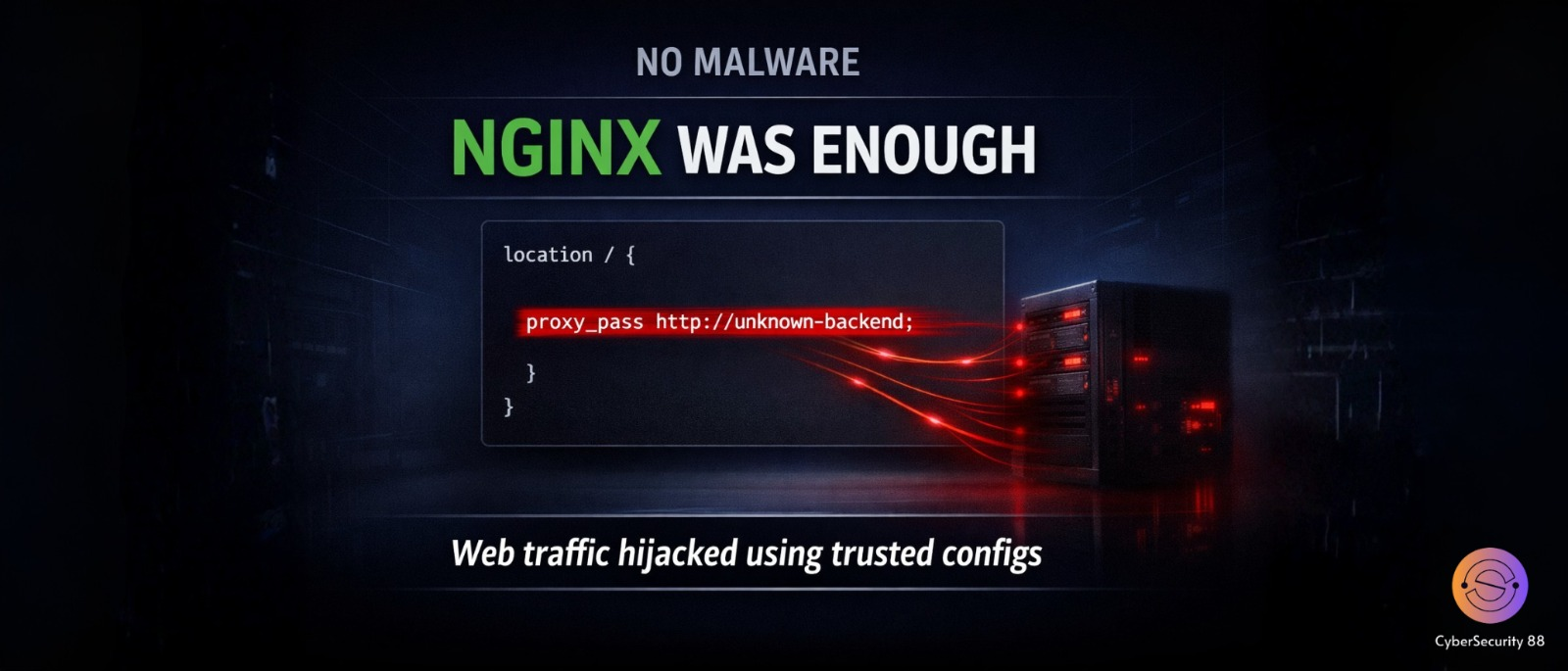
Malicious NGINX Configuration Abuse Enables Large-Scale, Stealth Web Traffic Hijacking Campaign
February 05, 2026
Cybersecurity researchers have uncovered a large-scale attack campaign where hackers are abusing ...
Read More >
Ransomware Is Becoming Organized Crime: Inside the Rise of Cartel-Driven Cyber Attacks
February 05, 2026
A ransomware group named DragonForce has started behaving very differently from other cybercrimin...
Read More >
AI Accelerates Cloud Attacks: Full AWS Environment Compromised in Just Eight Minutes
February 04, 2026
A recent cybersecurity incident has revealed how artificial intelligence can dramatically speed u...
Read More >
From Disclosure to Exploitation: Russian-Linked Hackers Abuse Microsoft Office Flaw Just Days After Patch Release
February 04, 2026
A serious security flaw was recently discovered in Microsoft Office, and hackers moved extremely ...
Read More >

