Search for topics
Trending Searches
Featured Articles

UNC6426 Exploits Nx npm Supply-Chain Attack to Gain AWS Administrator Access in Just 72 Hours
March 11, 2026
A recent cybersecurity investigation revealed how a threat actor called UNC6426 managed to compro...
Read More >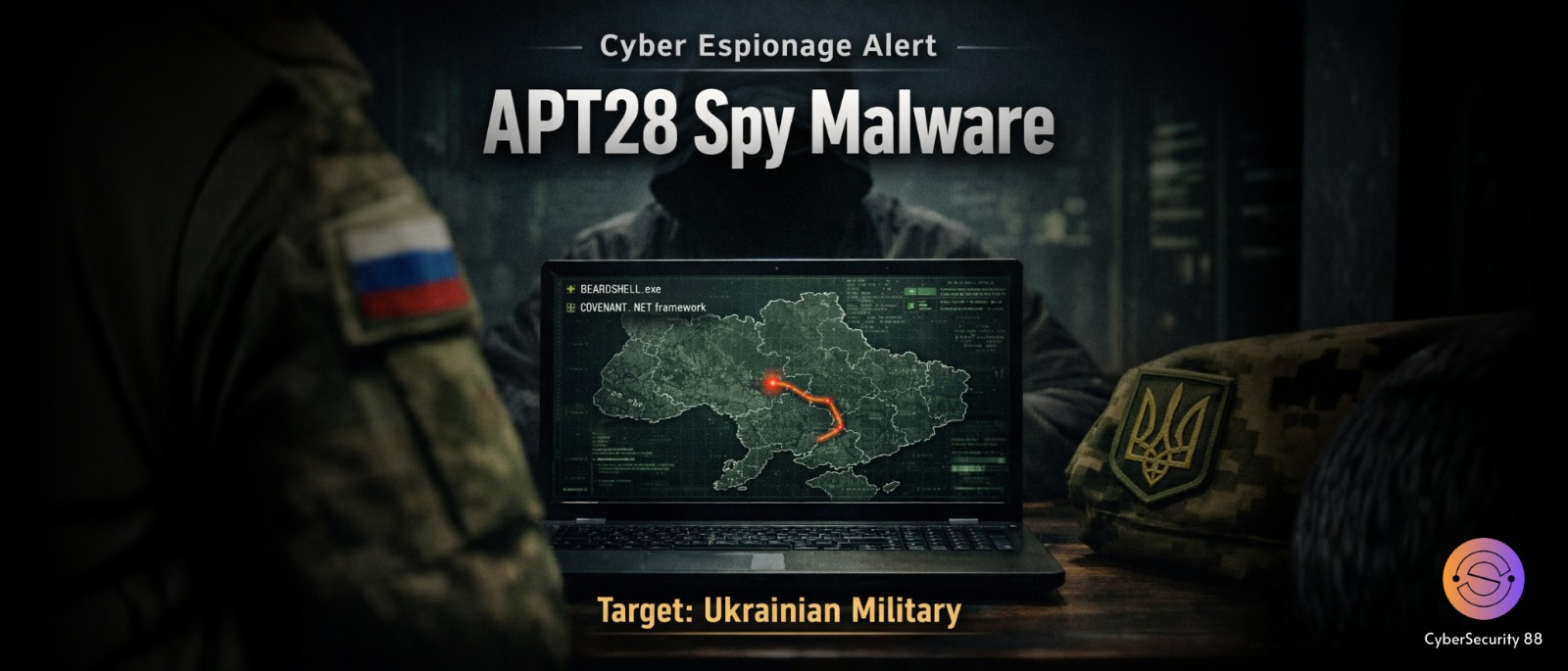
Russian-Linked APT28 Uses BEARDSHELL Backdoor and COVENANT Framework in Ukraine Cyber Espionage Campaign
March 10, 2026
Cybersecurity researchers have discovered a new cyber-espionage campaign targeting Ukrainian mili...
Read More >
India’s Cybersecurity Spending Expected to Reach $3.4 Billion by 2026 as AI-Powered Cyber Threats Continue to Grow
March 10, 2026
India’s cybersecurity spending is expected to grow significantly as organizations face more adv...
Read More >
Malicious Chrome Extension Discovered After Developer Ownership Transfer
March 09, 2026
Cybersecurity researchers have recently discovered a serious security issue involving a Google Ch...
Read More >
Web Server Exploits and Mimikatz Used in Cyberattacks Targeting Asian Critical Infrastructure
March 09, 2026
Cybersecurity researchers recently discovered a new cyberattack campaign targeting critical infra...
Read More >
Iran-Linked MuddyWater Hackers Deploy New “Dindoor” Backdoor to Target U.S. Networks
March 06, 2026
Cybersecurity researchers have recently uncovered a new cyber campaign linked to the Iranian hack...
Read More >
Microsoft Warns of ClickFix Attack Using Windows Terminal to Deploy Lumma Stealer
March 06, 2026
Microsoft has recently revealed details about a new cyberattack campaign that is using a social-e...
Read More >

