Security experts have identified that malicious actors are currently taking advantage of a security weakness in ChatGPT, enabling them to insert harmful URL redirects within the AI chatbot’s interface. In just one week, over 10,000 exploitation attempts were traced back to a single malicious IP addresses
What is it
Security analysts uncovered this vulnerability within OpenAI’s ChatGPT framework, officially designated as CVE-2024-27564 (with a CVSS rating of 6.5). Despite limited public awareness of this issue—likely due to its “medium severity” classification—attackers are demonstrating significant interest in exploiting it.
The research indicates that approximately 35% of examined organizations face elevated risk due to improper configurations in their defensive systems, including intrusion prevention systems, web application firewalls, and general firewall settings.
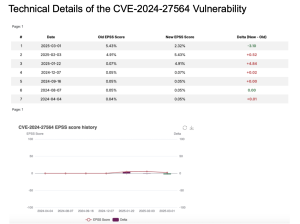
Technical Details of the CVE-2024-27564 Vulnerability
The National Vulnerability Database maintained by the National Institute of Standards and Technology identifies CVE-2024-27564 as a server-side request forgery (SSRF) vulnerability located in the pictureproxy.php component of ChatGPT commit f9f4bbc. According to the official description, this flaw “enables attackers to compel the application to generate arbitrary requests through the injection of specially crafted URLs into the url parameter.”
Essentially, this weakness allows malicious actors to introduce harmful URLs into ChatGPT’s input fields, forcing the system to execute unintended requests. Video documentation demonstrating this exploitation technique is accessible on YouTube.
The video : https://www.youtube.com/watch?v=R9zsRGYc2PA
Impact
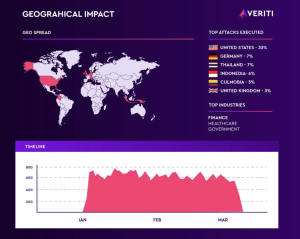
Geographic analysis shows that 33% of the over 10,000 attack attempts occurred within the United States, while Germany and Thailand each accounted for 7%. Additional targets included organizations in Indonesia, Colombia, and the United Kingdom. While financial institutions represented the most frequently targeted sector, government agencies and healthcare organizations also faced significant attack attempts
Security researchers suggest that financial organizations likely represent prime targets due to their extensive implementation of AI-powered services and API integrations, “creating vulnerabilities to SSRF attacks that can access internal resources or extract sensitive information.” Successful attacks against these entities could potentially result in various negative consequences, including unauthorized financial transactions, regulatory violations and penalties, and substantial reputational damage
Remediation
Add the following IPs to your firewall or monitor their interactions with your IT infrastructure, as they are currently exploiting CVE-2024-27564.
31.56.56[.]156
38.60.191[.]7
94.156.177[.]106
159.192.123[.]190
119.82.255[.]34
103.251.223[.]127
104.143.229[.]115
114.10.44[.]40
116.212.150[.]192
145.223.59[.]188
167.100.106[.]99
174.138.27[.]119
212.237.124[.]38
216.158.205[.]221
Conclusion
As users interact with Generative AI, sensitive data is often shared and processed, which could lead to significant risks and potential catastrophes. Strengthening security measures and implementing stringent policies for its use is essential. This will be a crucial long-term strategy to avoid data breaches.
Follow us on X and Linkedin for the latest cybersecurity news.
Source:hxxps[://]veriti[.]ai/blog/cve-2024-27564-actively-exploited/