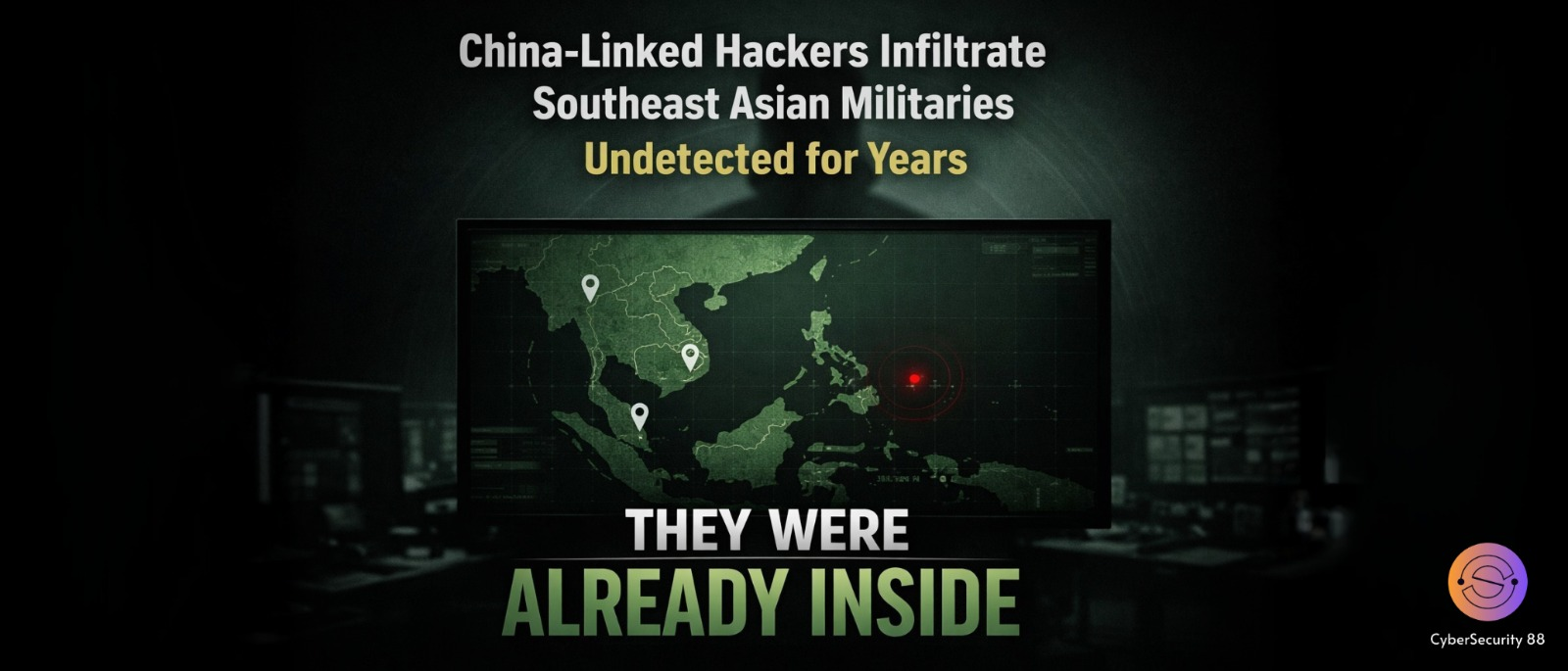
A recent cybersecurity investigation has revealed a serious and long-running cyber espionage campaign targeting military organizations in Southeast Asia. Researchers from Palo Alto Networks’ Unit 42 found that hackers linked to China secretly accessed sensitive systems. They managed to stay hidden inside these networks for several years without being detected. This shows how advanced and dangerous modern cyber threats have become.

The investigation showed that the hackers had been active since at least 2020. Instead of launching quick attacks, they focused on maintaining long-term access. Their goal was to quietly collect important information over time. This included military data, internal structures, and details about cooperation with Western defense groups.
What makes this attack more concerning is the level of planning involved. The hackers used specially designed malware tools to carry out their operations. These tools helped them enter systems and stay there without raising suspicion. Their approach was careful, slow, and focused on avoiding detection at all costs.
Two major tools used in the attack were named “AppleChris” and “MemFun.” These acted as backdoors, allowing attackers to control infected systems remotely. They also used a credential-stealing tool to collect login information. This helped them move deeper into networks and access more sensitive data.
Another advanced method used in this campaign was called “dead-drop resolvers” (DDR). In this technique, hackers hide instructions inside normal websites. The malware then collects this hidden data instead of directly contacting a server. This makes the activity look normal and helps attackers avoid detection.
The hackers even used public platforms like Pastebin to store encrypted information. This allowed them to secretly communicate with infected systems. Because these platforms are commonly used, the activity did not appear suspicious. This made it harder for security systems to identify the threat.
Researchers have tracked this activity under the name CL-STA-1087. Although the exact group is not officially confirmed, it is believed to be linked to Chinese state-sponsored actors. These types of attackers are known as Advanced Persistent Threats (APTs). They are highly skilled and focus on long-term cyber espionage operations.
This case clearly shows how cyber warfare is changing over time. The attackers used patience and smart techniques instead of quick attacks. By staying hidden, they were able to collect valuable intelligence for years. It highlights the need for stronger cybersecurity to protect sensitive systems from such threats.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news