A major international law-enforcement operation has shut down Tycoon 2FA, a phishing-as-a-service platform used by cybercriminals to steal login credentials and bypass security protections. The operation was led by Europol with support from several cybersecurity companies and technology partners. Authorities targeted the infrastructure that powered the service. As a result, many domains used for phishing attacks were seized and taken offline.

Tycoon 2FA was a subscription-based phishing toolkit that allowed criminals to launch attacks without needing advanced technical knowledge. Users of the service could create fake login pages and phishing campaigns through a ready-made dashboard. These pages were designed to look almost identical to legitimate websites. Once victims entered their details, the information was captured and sent directly to attackers.
The phishing platform first appeared around 2023 and quickly became widely used in the cybercrime ecosystem. Security researchers later connected the platform to more than 64,000 phishing attacks across the internet. The service operated through thousands of malicious domains hosting phishing pages. These sites were used to collect usernames, passwords, and authentication information from victims.
Investigations revealed that Tycoon 2FA was responsible for sending tens of millions of phishing emails every month. These campaigns targeted organizations in sectors such as healthcare, education, government, finance, and non-profits. In some periods, phishing emails connected to the platform were sent to over 500,000 organizations worldwide. This showed the large scale and reach of the operation.
Researchers also found that attackers gained unauthorized access to nearly 100,000 organizations globally through campaigns linked to the platform. Security data showed the service was responsible for more than 60 percent of phishing attempts blocked by Microsoft systems by mid-2025. In one month alone, over 30 million phishing emails connected to the platform were stopped. Overall, around 96,000 victims have been linked to Tycoon 2FA attacks.
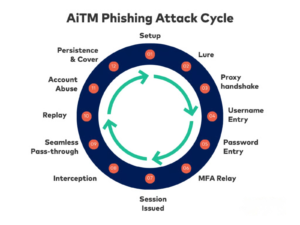
One of the main reasons the platform was successful was its ability to bypass multi-factor authentication. The phishing kit used a technique known as Adversary-in-the-Middle (AiTM) attacks. Victims were redirected to fake login pages that acted as a bridge between the user and the real service. When credentials and MFA codes were entered, the system captured them while passing the login request to the real website.
This method allowed attackers to steal authentication tokens and session cookies. With these tokens, criminals could access the victim’s account even after MFA verification was completed. Many phishing pages created by Tycoon 2FA mimicked popular services like Microsoft 365, Outlook, OneDrive, Gmail, and SharePoint. Because the pages looked genuine, many users were tricked into entering their login details.
The platform also used several techniques to avoid detection and remain active. Phishing domains were often active for only 24 to 72 hours before being replaced with new ones. This fast domain rotation made it harder for security systems to block the attacks quickly. Law-enforcement agencies from multiple countries worked together to seize around 330 domains, disrupting one of the most active phishing platforms operating online.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news