Trend Research has revealed that a September 2024 security update by NVIDIA left a critical vulnerability (CVE-2024-0132) in the NVIDIA Container Toolkit only partially patched — putting systems at risk of container escape attacks.
NVIDIA Patch Falls Short
In September 2024, NVIDIA released a security update to fix CVE-2024-0132, a critical vulnerability in the NVIDIA Container Toolkit with a CVSS v3.1 severity rating of 9.0.
However, security researchers at Trend Research later discovered that the fix was incomplete. Their October 2024 analysis revealed that the patched versions still contained a time-of-check to time-of-use (TOCTOU) race condition. This vulnerability enables specially crafted containers to access the host file system by exploiting a gap between permission verification and resource access.
The vulnerability affects:
- Toolkit versions 1.17.3 and earlier — vulnerable by default.
- Version 1.17.4 — vulnerable if the feature
allow-cuda-compat-libs-from-containeris enabled. - This issue has been cataloged under ZDI-25-087.
Why it matters
Organizations running AI workloads or containerized cloud infrastructure — especially those using default configurations — could be exposed to:
- Unauthorized access to sensitive host data
- Theft of AI models or IP
- Operational disruptions
- Denial-of-service (DoS) incidents
Docker’s Denial-of-Service Issue
Trend Analysis also uncovered a performance related issues in Docker on Linux systems, which can cause DoS attacks. This issue stems from how Docker handles mount propagation when containers are created using bind-propagation=shared.
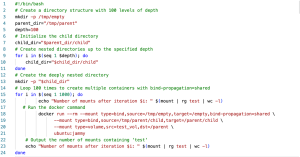
When these containers terminate, the associate mount table entires are not removed properly. Over time, this results in results in large mount table, exhaustring file descpritons and degrading perfoamce to the point where
- New containers cannot be created
- SSH access to host becomes impossible
- High CPU usage
Both Moby (the open-source container project behind Docker) and NVIDIA independently confirmed the issue to Trend Micro.
How an Attack Might Work
A potential exploitation scenario involves:
-
- Creating two malicious container images linked via a volume symlink.
- Deploying them on a target system — either directly or through a supply chain or social engineering attack.
- Exploiting the TOCTOU vulnerability to gain unauthorized access to the host system.
- Using access to the Docker container runtime sockets to execute commands as root, effectively taking control of the host
Successful exploitation could result in
- Theft of intellectual property and AI models
- Complete host compromise
- Business disruptions due to system unavailability or performance degradation.
Conclusion
Enterprises using AI, containerized applications, or hybrid cloud environments — particularly those relying on default Docker or NVIDIA toolkit configurations — are at heightened risk.
As of now, there is no evidence of exploitation in the wild. However, a proof-of-concept (PoC) has been publicly disclosed, increasing the risk that threat actors may attempt to develop working exploits — especially in the absence of complete patches.
While definitive patches are still pending, organizations should Restrict Docker API access and Disable non-essential or experimental toolkit features. Moreover, Monitor the Linux mount table for abnormal growth or uncleaned entries that could signal a brewing DoS condition.
Source: hxxps[://]www[.]trendmicro[.]com/en_us/research/25/d/incomplete-nvidia-patch.html
Follow us on X and Linkedin for the latest cybersecurity news