Cybersecurity researchers have uncovered a new supply chain attack involving 26 malicious npm packages published to the public registry. These packages were disguised as normal developer tools but secretly contained harmful code. The activity has been linked to threat actors associated with North Korea. The campaign specifically targeted developers and software environments.
Researchers have named this operation “StegaBin” because of the unusual method used to hide its command-and-control infrastructure. Instead of placing server addresses directly in the code, the attackers hid them inside Pastebin posts. The hidden data was concealed using character-level steganography. To anyone reading the text, it looked like harmless technical content.
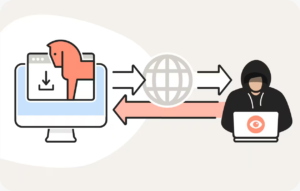
When one of these npm packages was installed, it automatically executed a hidden script during setup. This script quietly contacted Pastebin to retrieve the concealed instructions. After decoding the hidden information, it identified the attacker-controlled servers. The entire process happened silently in the background.
Once the command infrastructure was discovered, the package downloaded additional malicious components. Researchers observed that the final payload included a cross-platform Remote Access Trojan (RAT). It also deployed a multi-module credential stealer. These tools were designed to operate on Windows, macOS, and Linux systems.
The Remote Access Trojan allowed attackers to control infected machines remotely. This meant they could execute commands and access files without the victim’s knowledge. The credential stealer targeted sensitive data such as SSH keys and stored browser credentials. Such information could later be used for deeper network access or financial theft.

Investigators found that the malicious infrastructure was hosted using platforms such as Vercel. While Vercel is a legitimate hosting service, it was abused in this campaign to deliver payloads. The attackers used staged downloads to avoid easy detection. This multi-step design made traditional scanning tools less effective.
Security experts noted that the campaign also relied on typosquatting techniques. Some malicious package names closely resembled legitimate npm libraries to trick developers. In addition, the use of steganography helped conceal important details from automated analysis systems. These combined tactics show a high level of planning and technical sophistication.

This activity is believed to be part of a broader North Korean operation known for targeting developers through software supply chain attacks. Security professionals are urging teams to carefully audit npm dependencies. Monitoring unusual outbound connections and reviewing new packages before installation is strongly recommended. The incident once again highlights the growing risks facing the open-source ecosystem.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news