Yesterday morning, out of the blue, the notorious VanHelsing ransomware source code was suddenly listed for sale on the RAMP cybercrime forum.
This unexpected leak has quickly caught the attention of cybersecurity researchers and threat intelligence analysts, raising concerns about the potential misuse of the code and what it could mean for the organizations.
Initial Sale Attempt of VanHelsing
VanHelsing is a ransomware-as-a-service (RaaS) operation that launched in March 2025, advertising its ability to target a wide range of systems, including Windows, Linux, BSD, ARM, and ESXi. On RAMP, a user operating under the alias ‘th30c0der’ listed what appeared to be the source code for the VanHelsing affiliate panel, data leak Tor sites, and the builders for both Windows and Linux encryptors, all offered for $10,000.

However, the listing quickly caught the attention of the VanHelsing operators themselves. In response, the group publicly denounced as a former developer attempting to scam buyers. To invalidate the sale, the group decided to release a portion of the source code themselves.
What the Leak VanHelsing Contains
Despite the group’s effort to control the narrative, the source code dump appears to be incomplete. Notably absent are the Linux builder and any backend databases, crucial components that would have been particularly valuable to cybersecurity researchers and law enforcement agencies.
🚨 Van Helsing Ransomware source code Got Leaked. pic.twitter.com/XGfSfrXVK7
— CyberSecurity88 (@CSec88) May 21, 2025
According to BleepingComputer, which reviewed the leak, the released archive includes:
The Windows encryptor builder (confirmed as legitimate)
The affiliate panel and data leak site source code
A decryptor and loader
An early version of an MBR (Master Boot Record) locker, designed to overwrite the system’s bootloader with a ransom message
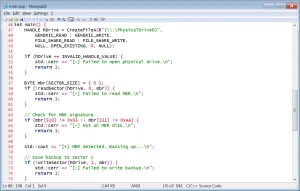
However, the source code is far from production-ready. The builder’s Visual Studio project files were oddly stored in the “Release” folder, a space typically reserved for compiled binaries.
Furthermore, the builder attempts to connect to the affiliate panel hosted at 31.222.238[.]208 to fetch configuration data (now defunct).
Still, because the source code for the panel is included in the leak, it’s likely that motivated actors could modify or recreate it to get the builder functioning again.
What Happens Next?
This isn’t the first time ransomware source code has been leaked and history tells us what tends to follow. When ransomware builders make their way into the wild, there’s usually a spike in activity from so-called “script kiddies” — inexperienced threat actors who repurpose leaked tools to launch attacks of their own.
In many cases, these repackaged versions of the original ransomware are sloppily executed but can still cause real damage, especially to underprepared targets. With the VanHelsing leak now public, we can expect to see copycats, new ransomware strains, and opportunistic actors attempting to monetize the source code even in its incomplete form.
The concerning part is that these inexperienced actors, lacking a proper understanding of how the ransomware actually works, could permanently delete the data.
Source: hxxps[://]www[.]bleepingcomputer[.]com/news/security/vanhelsing-ransomware-builder-leaked-on-hacking-forum/
Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news







