The cryptocurrency community is once again in the crosshairs of cybercriminals, according to a new report by ReversingLabs. In a series of ongoing attacks, threat actors are using increasingly stealthy methods to compromise Web3 wallets and siphon off crypto assets-this time by manipulating open-source packages.
The security researchers have identified a campaign involving a malicious npm package named pdf-to-office, which posed as a simple utility to convert PDF files to Microsoft Office formats. The package appeared innocuous but was instead designed to hijack local installations of widely used cryptocurrency wallets, including Atomic Wallet and Exodus Wallet.
Malicious Code Hidden in Plain Sight
While this method is not new, but attackers face the challenge of swift detection by the vast OSS developer community. Previous campaigns similar to this were short-lived due to rapid patching. As a result, threat actors are now adopting subtler techniques that allow malicious code to remain undetected for longer period.
In this campaign, the package was advertised as a PDFs to Office converter, its code didn’t support such features. Instead, it contained an obfuscated file that, once deobfuscated, revealed a trojanized payload.
This payload specifically targeted two popular crypto wallets:
- Atomic Wallet versions 2.90.6 and 2.91.5
- Exodus Wallet versions 25.9.2 and 25.13.3
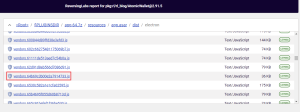
This package searcher for specific version files of these wallets and override them with trojanized versions that redirected outgoing cryptocurrency transactions to the attackers’ wallet address. In the case of Atomic Wallet, filenames such as a_2_90_6.js and a_2_91_5.js were used to match targeted versions. Similar tactics were employed to compromise the Exodus wallet by altering src/app/ui/index.js.
Notably, even if the pdf-to-office package was deleted, the modified wallet software remained compromised—ensuring persistent theft of funds until the entire wallet was removed and reinstalled.
Indicators of a Broader Campaign
This campaign is similar to earlier attacks in March, involving malicious npm packages ethers-provider2 and ethers-providerz. These acted as downloaders for second-stage payloads that similarly patched legitimate software, installing reverse shells and enabling remote access.
Further evidence suggests the attackers attempted to collect additional data or erase digital footprints. Researchers discovered zipped logs from the AnyDesk remote access tool being exfiltrated to a command-and-control server—indicating broader data theft or an effort to hinder forensic investigations.
The Bottom Line
While the official installers for Atomic Wallet and Exodus Wallet downloaded from their respective websites remain unaffected, the attack underscores the risks of compromised local environments and the increasingly sophisticated methods used by threat actors.
Follow us on X and Linkedin for the latest cybersecurity news








