A threat actor has successfully exploited a vulnerability in SentinelOne’s Endpoint Detection and Response (EDR) software to disable protections and deploy ransomware, according to a new disclosure from Aon’s Stroz Friedberg Incident Response Services.

The incident, uncovered during a forensic investigation, involved a method that bypassed SentinelOne’s anti-tamper protections by manipulating the agent upgrade and downgrade process. The flaw allowed the attacker to leave the endpoint unprotected without needing authorization typically required to alter or disable EDR functions. After successfully deactivating the EDR, the threat actor deployed a variant of the Babuk ransomware.
Breakdown of SentinelOne EDR Flaw
According to the report, the threat actor gained local administrative access to a publicly accessible server by exploiting a known vulnerability in a hosted application. They then initiated multiple legitimate SentinelOne installer files (SentinelOneInstaller_windows_64bit_v23_4_4_223.exeand SentinelInstaller_windows_64bit_v23_4_6_347.msi), triggering version changes within a 10-minute window.
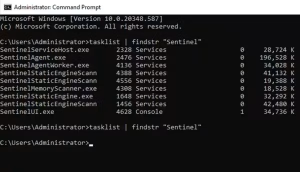
Logs showed product version swaps and termination of SentinelOne processes, followed by a system state with no active protection.

Stroz Friedberg concluded that the actor likely exploited a flaw in SentinelOne’s local upgrade process. The affected environment did not have the “online authorization” setting enabled, which would have restricted such local changes.
Stroz Friedberg replicated the scenario in a controlled test environment. They initiated an upgrade using a Windows MSI installer for SentinelOne and observed that all active SentinelOne processes were terminated during the version transition. By manually killing the msiexec.exe process before the new version could install, they left the system completely unprotected.
Mitigation of SentinelOne EDR Flaw
All SentinelOne users are urged to review their configuration settings and enable Online Authorization to prevent local upgrade-related vulnerabilities. SentinelOne collaborated with Stroz Friedberg to privately notify other EDR vendors ahead of the public disclosure, giving them time to assess and harden their own products.
As of publication, Stroz Friedberg reports no evidence that this bypass affects properly configured SentinelOne deployments or other vendors’ solutions.
If you need guidance on selecting an EDR solution, take a look at this Buyer’s Guide:Top 10 Endpoint Security Solutions in 2025.
Source: hxxps[://]www[.]aon[.]com/en/insights/cyber-labs/bring-your-own-installer-bypassing-sentinelone
Follow Cybersecurity88 on X and Linkedin for the latest cybersecurity news







