Cybersecurity researchers at Trend Micro have uncovered a significant evolution in the Agenda ransomware group, also known as Qilin, highlighting the group’s growing technical sophistication and expanding global footprint. First identified in July 2022, Agenda has steadily transformed into a formidable threat, now using advanced malware loaders, stealth tactics, and diverse distribution infrastructure.
Trend Micro findings reveals that Agenda ransomware has transitioned from its original Go-based implementation to the Rust programming language, improving its ability to evade detection, propagate in virtual environments, and execute remotely. In the first quarter of 2025, the group’s activity was primarily concentrated in the healthcare, technology, finance, and telecom sectors, affecting organizations in the U.S., Netherlands, Brazil, India, and the Philippines.

Agenda Ransomware Dropper- NETXLOADER
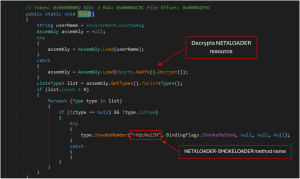
One of the most concerning developments is the discovery of NETXLOADER, a new .NET-based malware loader deployed in Agenda campaigns alongside SmokeLoader. First observed in November 2024, this loader acts as a launchpad for follow-up payloads, protected by .NET Reactor 6, which includes anti-disassembly and anti-debugging capabilities.
NETXLOADER’s infrastructure uses transient, dynamically generated domains such as bloglake7[.]cfd and mxbook17[.]cfdto host malicious payloads, mimicking benign services to avoid scrutiny. These domains deliver executables with deceptive names like rh10j0n.exe, which are renamed post-deployment to a standardized format (e.g., rh111.exe) to further reduce detection rates and obscure malware identities.
NETXLOADER employs complex techniques including JIT hooking, encrypted payloads, and obfuscated method names. It dynamically loads and executes malware in memory using system calls like VirtualAlloc, VirtualProtect, and CreateThread, bypassing traditional antivirus systems.
Agenda Ransomware Dropper- SmokeLoader
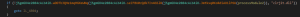
SmokeLoader, an established malware dropper, has been deployed in tandem with NETXLOADER to deliver the Agenda ransomware. The second-stage of SmokeLoader includes advanced anti-analysis techniques such as opaque predicates, dynamic API resolution, execution guardrails (e.g., avoiding Russian-language systems), and debugger evasion.
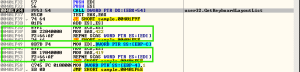
Its injection methods have evolved, now using shared memory sections and NtCreateSection to infiltrate explorer.exe. This version of SmokeLoader also contains robust sandbox and virtualization checks, looking for traces of analysis environments such as Sandboxes, VMware, and VirtualBox.
Once embedded, SmokeLoader monitors and terminates processes associated with common forensic and reverse engineering tools like IDA Pro,Process Explorer, Wireshark, and OllyDbg. It uses hashed values to identify both process names and window titles, ensuring persistent evasion.
Command-and-Control of Agenda Ransomware

SmokeLoader communicates with its command-and-control (C&C) servers via encrypted RC4 traffic, cloaked behind 404 responses that still carry hidden instructions. In this campaign, it connected to URLs like mxblog77[.]cfd/777/rh1jcr4[.]exe to download the final Agenda payload.

The final Agenda ransomware binary is loaded directly into memory using DLL reflective loading never touching disk which makes it difficult to intercept by endpoint.
Mitigation of Agenda Ransomware
Security experts recommend the following defenses
- Implement behavior-based detection that can flag memory injection and process hollowing tactics.
- Monitor network traffic for connections to newly registered, low-reputation domains.
- Use endpoint protection tools capable of detecting in-memory execution and encrypted loader behaviors.
- Employ threat intelligence feeds to block known malicious IPs and domains associated with Agenda ransomware and its distribution infrastructure.
Conclusion
This latest evolution demonstrates how Agenda ransomware continues to refine its methods to maximize impact and evade detection. By adopting Rust, the group gains flexibility in targeting diverse systems, including ESXi environments and cloud-based infrastructures. Their use of custom loaders and evasive infrastructure points to a highly coordinated effort to defeat even advanced security solutions.
Source: hxxps[://]www[.]trendmicro[.]com/en_us/research/25/e/agenda-ransomware-group-adds-smokeloader-and-netxloader-to-their.html
Follow Cybersecurity88 on X and Linkedin for the latest cybersecurity news







