A China-linked cyber threat actor, identified as Chaya_004, has been actively exploiting a critical vulnerability in SAP NetWeaver systems, according to new findings from cybersecurity firm Forescout Vedere Labs. The group is believed to be behind a growing wave of targeted attacks exploiting CVE-2025-31324, a recently disclosed security flaw that allows for remote code execution (RCE).

The vulnerability, which holds a maximum severity rating of CVSS 10.0, stems from an exposed endpoint—/developmentserver/metadatauploader—in SAP NetWeaver. Exploiting this vulnerability enables attackers to upload web shells and execute arbitrary code remotely.
CVE-2025-31324 Exploitation
First flagged by ReliaQuest in late April, CVE-2025-31324 has already been weaponized in real-world attacks. The flaw has been used to deploy both custom web shells and the Brute Ratel C4 post-exploitation toolkit, with hundreds of SAP systems reportedly compromised across a broad spectrum of sectors. According to SAP security firm Onapsis, victims span industries including energy, manufacturing, government, pharmaceuticals, retail, and media.
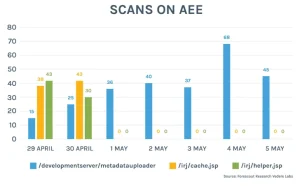
Since March, multiple threat actors have jumped on the opportunity to exploit vulnerable systems for various purposes, including web shell deployment and cryptocurrency mining.
Threat-Actor Chaya
Forescout has linked Chaya_004 to an IP address (47.97.42[.]177) hosting SuperShell, a Golang-based reverse shell. The address was extracted from a malicious ELF binary named config used in the attack. The use of Chinese cloud services and Chinese-language hacking tools has led researchers to attribute the campaign to a threat actor likely operating from China.
A notable red flag was an anomalous self-signed SSL certificate impersonating Cloudflare, detected on port 3232 of the same IP, adding to the mounting evidence linking the infrastructure to advanced malicious operations.
Further investigation revealed the IP also hosted several tools and services commonly used by advanced persistent threat groups, including Cobalt Strike, NPS, SoftEther VPN, Asset Reconnaissance Lighthouse (ARL), Pocassist, GOSINT, and GO Simple Tunnel.
Conclusion
Security experts urge immediate patching of CVE-2025-31324. Recommended mitigation steps include restricting access to the vulnerable metadata uploader endpoint, disabling the Visual Composer service if not in use, and continuous monitoring for suspicious behavior within SAP environments.
Follow Cybersecurity88 on X and Linkedin for the latest cybersecurity news







