A persistent cyber-espionage operation tied to Russia’s military intelligence agency has been targeting high-level Ukrainian officials and foreign defense contractors supplying arms to Kyiv, new research reveals.

Security analysts at ESET report that the hacking group fancy bear, widely attributed to Russia’s GRU—has been conducting an aggressive cyberespionage campaign since at least 2023. The operation relies on spearphishing emails and exploits in popular webmail platforms like Roundcube, Horde, MDaemon, and Zimbra.
One of the vulnerabilities exploited was a zero-day—CVE-2024-11182—used in a targeted phishing wave in November 2024. This vulnerability had not been publicly documented prior to its use. Researchers say the group appears to be the only known entity leveraging the exploit, suggesting it was either developed in-house or acquired through underground vendors.
Other vulnerabilities used in the campaign were previously known and had available security patches, but the group demonstrated a sustained interest in exploiting webmail platforms to breach sensitive communications.
How the attacks work
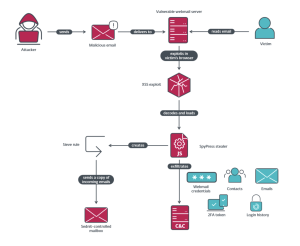
The operation primarily used phishing emails laced with malicious scripts exploiting email software vulnerabilities. In several cases, researchers confirmed that security defenses blocked the attempts at various stages either by intercepting the emails, preventing the malware from running, or cutting off data exfiltration.
The phishing emails often contained fake headlines from Ukrainian news sources, written in Ukrainian, to create a sense of urgency or relevance. Topics ranged from alleged arrests of Russian spies in Ukraine to international political developments involving Russia.
Who was targeted
The attackers focused on Ukrainian government agencies, military personnel, and defense contractors both inside Ukraine and in countries like Romania and Bulgaria. Victims also included officials and entities in Greece, Serbia, Cameroon, Ecuador, and elsewhere.
In total, researchers linked at least 17 distinct organizations to the ongoing campaign in 2024. Most of the targets had ties to the defense sector or government institutions with a strategic interest in the ongoing Russia-Ukraine conflict.
While the campaign’s main aim appears to be intelligence-gathering on Ukraine’s military supply chain, researchers found signs of broader surveillance across Latin America, Europe, and Africa.
The bottom line
The campaign underscores a continued focus by Russian-linked cyber actors on extracting sensitive military and political intelligence related to the Ukraine conflict. As the war continues, cybersecurity experts warn that such operations are likely to intensify and expand in scope.
Source: hxxps[://]www[.]welivesecurity[.]com/en/eset-research/operation-roundpress/
Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news