A serious security issue has been discovered in Ubuntu, and it is gaining attention in the cybersecurity community. The vulnerability is identified as CVE-2026-3888 and mainly affects Ubuntu Desktop systems from version 24.04 onwards. This flaw is dangerous because it allows an attacker with limited access to gain full root privileges. Root access means complete control over the entire system.
This vulnerability was discovered by security researchers at Qualys during their analysis. It has been given a high severity rating with a CVSS score of 7.8. Even though the attacker starts with low-level access, they can slowly escalate their privileges. This makes the vulnerability especially risky in shared or multi-user environments.
The main reason behind this issue is the interaction between two system components. The first is snap-confine, which manages sandboxing for snap applications. The second is systemd-tmpfiles, which handles automatic cleanup of temporary files. Both are safe individually, but together they create a timing-based weakness.
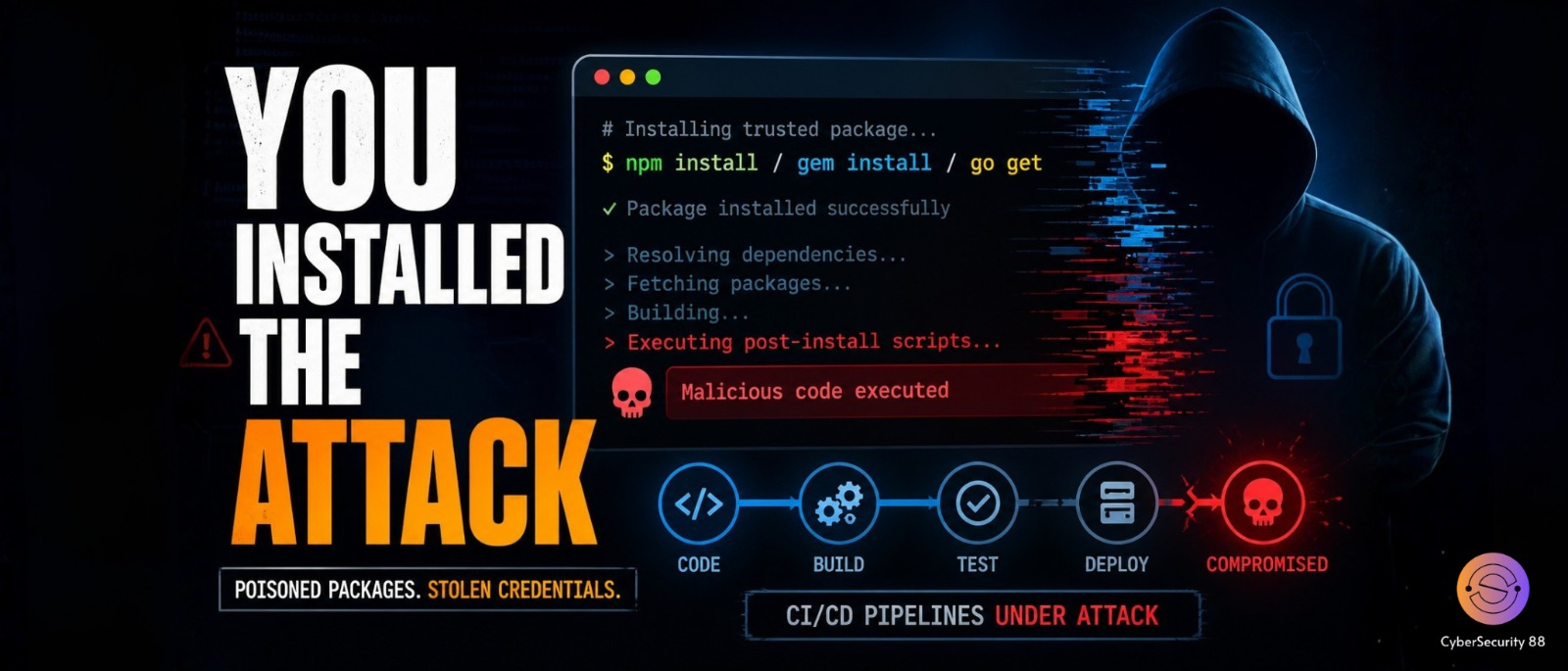
The attack works in a simple but smart way and does not require complex steps. Ubuntu automatically deletes old files from the /tmp directory after a certain number of days. During this cleanup, an important directory used by snap-confine may get removed. This creates an opportunity for the attacker to act.
Once the directory is deleted, the attacker quickly recreates it with malicious content. These files are placed in a way that tricks the system into trusting them. When a snap application runs again, the system may load these files. Since snap-confine runs with higher privileges, the attacker’s code gets executed as root.
One important point is that this attack does not need any user interaction. It also works silently in the background without showing clear warning signs. The only requirement is time, as the attacker must wait for the cleanup process. But once successful, the attacker gains complete control over the system.
This vulnerability mainly affects Ubuntu Desktop 24.04 and newer versions using snapd. Older versions are generally safe unless configured in a similar way. To fix the issue, Ubuntu has released updates for snapd. Versions below 2.73 and 2.74.1 are affected and should be updated immediately.
Researchers also found another issue in the uutils coreutils package during their study. This bug could allow misuse of symbolic links to delete files as root. Although it has already been fixed in newer releases, it adds to the overall risk. This case shows how small issues can combine into serious security problems.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news