Germany’s Federal Criminal Police Office, known as Bundeskriminalamt (BKA), has identified the main people behind the REvil ransomware group. This group was responsible for at least 130 ransomware attacks in Germany between 2019 and 2021. The investigation marks a major step in uncovering cybercriminals who usually operate anonymously. These attacks affected multiple organizations and caused serious disruptions. It also shows how advanced cybercrime has become in recent years.
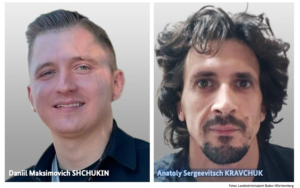
The investigation revealed that one of the key individuals is Daniil Maksimovich Shchukin, a 31-year-old Russian national. He was known online by the alias “UNKN” (Unknown) and used several other names like Oneiilk2 and GandCrab. Authorities believe he played a leadership role in the REvil operation. This group is considered one of the most dangerous ransomware groups globally. Another suspect identified is Anatoly Sergeevitsch Kravchuk, who is believed to be linked to the same network.
The attacks carried out by this group were highly organized and targeted different companies and institutions. They used ransomware to lock systems and demanded money to restore access. In many cases, they also stole sensitive data from the victims. They threatened to release this data publicly if the ransom was not paid. This method is commonly known as double extortion and is widely used in modern cyberattacks.
The financial damage caused by these attacks was very significant for the victims. Reports show that around €2 million was paid directly as ransom to the attackers. However, the total economic damage is estimated to be more than €35 million. This includes losses due to downtime, recovery efforts, and reputational harm. Many organizations faced serious operational challenges during and after the attacks. The impact was not just financial but also affected trust and business continuity.
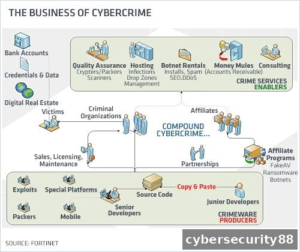
The REvil group operated using a Ransomware-as-a-Service model, which made it more dangerous. In this model, they developed ransomware and allowed other criminals to use it. These affiliates carried out attacks and shared a portion of the profits with the developers. This system made it easier for more attackers to join and launch cyberattacks. As a result, the scale and frequency of attacks increased rapidly. It became a major threat globally due to this structured approach.
The group was mainly active between 2019 and 2021, during which it carried out multiple attacks worldwide. Even after the group became inactive, investigations continued by authorities. Tracking such cybercriminals takes time due to their use of hidden identities and global networks. The recent identification shows that law enforcement efforts are still ongoing. It also proves that these cases are not forgotten even after years. Authorities continue to work across borders to find those responsible.
According to the BKA, the main suspect acted as a leader of one of the largest ransomware groups. He was involved in demanding large ransom payments from victims across different regions. This highlights the scale at which the group was operating. Identifying such individuals is a complex task due to international challenges. Cybercriminals often use advanced tools to stay hidden and avoid detection. Despite this, investigators were able to trace key individuals involved.
Overall, this case is an important development in the fight against cybercrime. It shows that even large and hidden cybercriminal groups can be exposed over time. The identification of these individuals sends a strong message to other attackers. It also highlights the growing need for strong cybersecurity measures. Organizations must stay prepared to handle such threats effectively. This case reflects both the risks of cyberattacks and the progress in tackling them.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news