A new cybersecurity report has revealed a dangerous technique being used by ransomware groups like Qilin and Warlock. These groups are no longer just breaking into systems to encrypt files, but are first targeting the security systems themselves. Their main goal is to disable protection tools so that they can operate without being detected. This shift makes the attacks more powerful and harder to stop. It also shows how ransomware tactics are evolving rapidly.
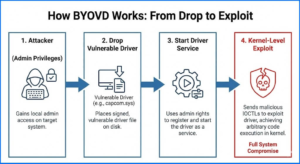
Researchers from Cisco Talos and Trend Micro discovered that these attackers are using a method called Bring Your Own Vulnerable Driver (BYOVD). In this technique, hackers install legitimate but vulnerable drivers on a system and then exploit them. Since these drivers are already trusted and signed, they usually do not trigger security warnings. This allows attackers to gain deep access to the system without raising suspicion. As a result, they can bypass many modern security protections.
The Qilin ransomware attack follows a carefully designed multi-stage process. It starts with a malicious file named msimg32.dll, which is loaded using DLL side-loading. Inside this file, there is an encrypted payload designed to disable security tools. The payload runs directly in memory, which makes it harder to detect using traditional methods. This approach helps the malware stay hidden while preparing for further actions.
Once active, the malware can disable more than 300 EDR drivers used by major security vendors. It removes monitoring hooks that security tools rely on to track activity. It also blocks Windows logging systems like Event Tracing for Windows, making it difficult to record malicious actions. Additionally, the malware hides its own processes to avoid detection. This combination of actions makes the system almost completely blind.
The attack also makes use of vulnerable drivers such as rwdrv.sys and hlpdrv.sys. These drivers allow attackers to access system memory and terminate important security processes. Before shutting down protection tools, the malware removes system callbacks that could interfere with its actions. This ensures that nothing can stop the attack once it starts. Such deep control over the system makes the attack extremely dangerous.
Another serious aspect of this attack is the delayed execution of ransomware. Instead of attacking immediately, the hackers stay inside the system for several days. During this time, they expand their access, gather information, and prepare for maximum impact. On average, the ransomware is deployed after about six days. This delay makes detection much harder and increases the overall damage caused.
The Qilin group is currently one of the most active ransomware operators in the world. Many of their attacks begin with stolen login credentials, which allow them to enter systems quietly. This method helps them avoid detection during the initial stage of the attack. Their ability to remain hidden for long periods makes them a serious threat. It also shows how well-planned their operations have become.
At the same time, the Warlock ransomware group is also evolving quickly. It has been seen targeting unpatched Microsoft SharePoint servers to gain access. Warlock also uses vulnerable drivers like NSecKrnl.sys as part of the BYOVD technique. The group uses tools like PsExec, TightVNC, and Rclone to move inside networks and steal data. In some cases, it even uses Cloudflare Tunnel and Visual Studio Code to maintain hidden communication channels, making detection even more difficult.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news