\A new Android malware called Mirax has recently been discovered and is raising serious concerns in cybersecurity. It works as a Remote Access Trojan, allowing attackers to control infected devices remotely. Researchers found that it is being spread through advertisements on Meta platforms. These include Facebook, Instagram, Messenger, and Threads. Because of this wide reach, the campaign has already impacted more than 220,000 users.

Mirax is not a simple malware and comes with advanced features. Once a device is infected, attackers can monitor user activity in real time. They can also perform actions on the device without the user knowing. The malware runs silently in the background, making it difficult to detect. This allows attackers to stay hidden for a long time.
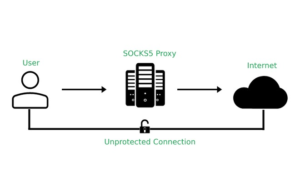
One of the most unique features of Mirax is its ability to turn infected devices into residential proxy nodes. It uses the SOCKS5 protocol to route traffic through the victim’s internet connection. This makes the attacker’s activity look normal and harder to trace. It also helps them bypass geo-restrictions and security systems. This feature makes Mirax more dangerous than traditional malware.
The malware is also being sold as a service on underground forums. It is reportedly priced at around $2,500 for a three-month subscription. A cheaper version is also available with fewer features. Access to this malware is restricted and mainly given to experienced cybercriminals. This shows that the operation is organized and professional.
Mirax has several spying and data theft capabilities. It can record keystrokes, steal photos, and collect lock screen details. It can also monitor user behavior and execute commands on the device. Another dangerous feature is the use of fake overlay screens. These overlays trick users into entering sensitive information like login credentials.
The malware is mainly spread through fake apps promoted via Meta ads. These ads often promote free streaming services such as movies or live sports. When users click on them, they are redirected to malicious websites. These sites convince users to download harmful apps. Many of these apps appear as normal video players or streaming tools.
To avoid detection, Mirax uses advanced installation techniques. It checks whether the device is real and tries to bypass security systems. The infection process happens in multiple stages, making it harder to detect. After installation, it asks users to enable accessibility permissions. Once granted, it gains deeper control over the device.
After becoming active, Mirax connects to command-and-control servers through different channels. These channels allow attackers to send commands and collect data. It also sets up SOCKS5 proxy connections on specific ports. This turns infected devices into part of a larger proxy network. Overall, this malware shows how cyber threats are becoming more advanced and dangerous.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news