A new cyberattack called “Mini Shai-Hulud” has been discovered and is linked to a group known as TeamPCP. This attack mainly targets software packages used in SAP development environments. Instead of directly hacking systems, the attackers chose a smarter approach by compromising trusted tools. These tools are used daily by developers, which makes the attack more dangerous. It shows how modern cyber threats are shifting toward supply chain attacks.

The attack focuses on npm packages that are commonly used in SAP-related projects. Security researchers found that some of these packages were secretly modified to include hidden malicious code. Since developers trust these packages, they install them without thinking twice. This allows the malware to spread silently across systems. As a result, many users get affected without even realizing it.
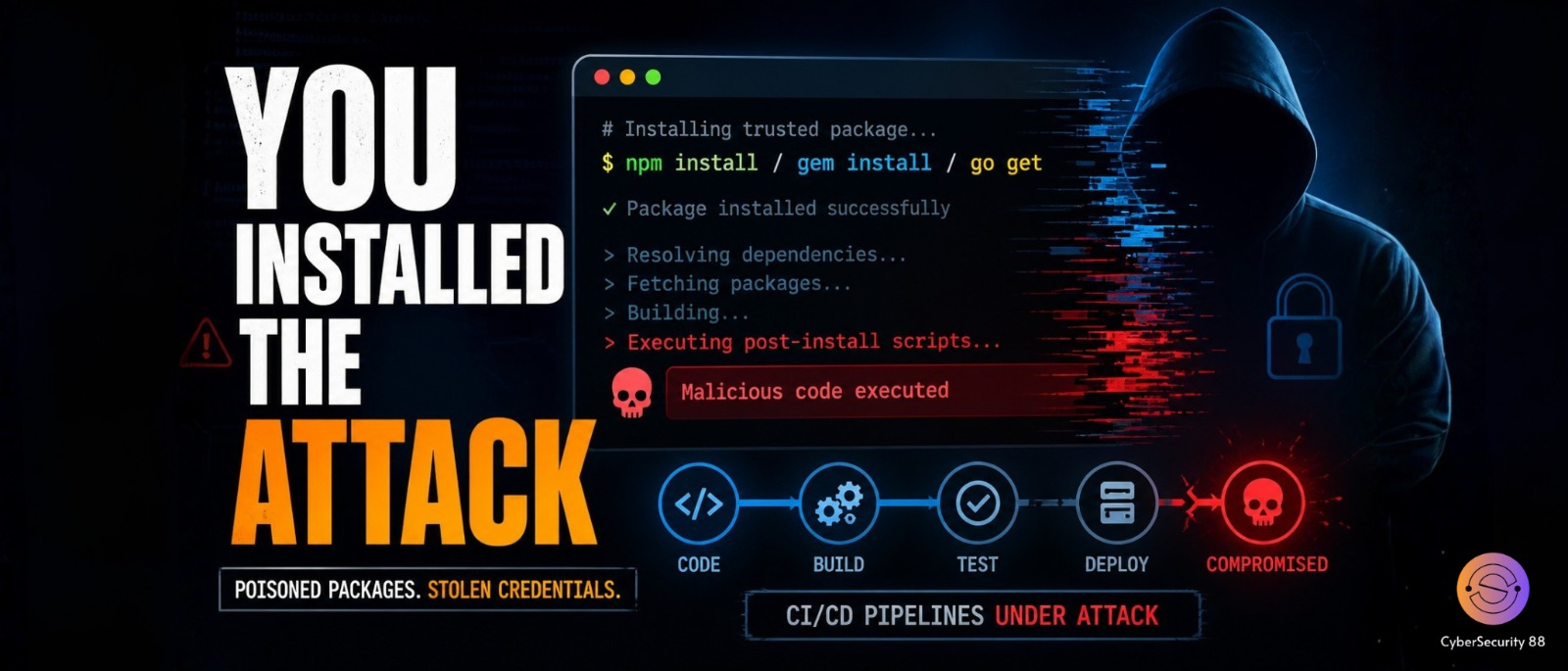
The main technique used in this attack involves something called a preinstall script. This script runs automatically when the package is installed on a system. Once executed, it downloads an additional hidden payload in the background. The payload then runs on the system without the user noticing anything unusual. This makes the attack very hard to detect during normal usage.
After the malware is active, it starts collecting sensitive data from the infected system. This includes GitHub tokens, npm credentials, and cloud service keys like AWS, Azure, and Google Cloud. These credentials are very valuable because they provide access to important systems. The stolen data is then sent to attacker-controlled servers. In some cases, GitHub repositories are used to store this stolen information.
One of the most dangerous features of this attack is its ability to spread on its own. Using stolen credentials, the malware can access other projects and inject malicious code into them. It can also publish new infected versions of packages automatically. This behavior makes it similar to a worm, increasing its reach quickly. As a result, more developers and systems get compromised over time.
Initially, the attack targeted SAP-related packages such as @cap-js/db-service, @cap-js/postgres, @cap-js/sqlite, and mbt. However, it later expanded beyond SAP environments into other ecosystems. Researchers found similar infections in a Python package called lightning. It also affected npm and PHP packages related to intercom. This expansion shows how quickly the attack can spread across platforms.
The impact of this attack has been significant in a short period of time. Reports indicate that more than 1,800 developers were affected by this campaign. Many repositories were compromised, and some infected packages had millions of downloads. In several cases, attackers even left a message saying “A Mini Shai-Hulud has Appeared.” This highlights both the scale and confidence of the attackers.
This attack is especially dangerous because it targets the software supply chain. Developers usually trust the tools they use, which makes detection difficult. There is no phishing or suspicious activity involved, as everything happens during normal installation. Experts advise developers to check systems, rotate credentials, and update packages immediately. Overall, this attack shows a major shift in modern cybersecurity threats.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news