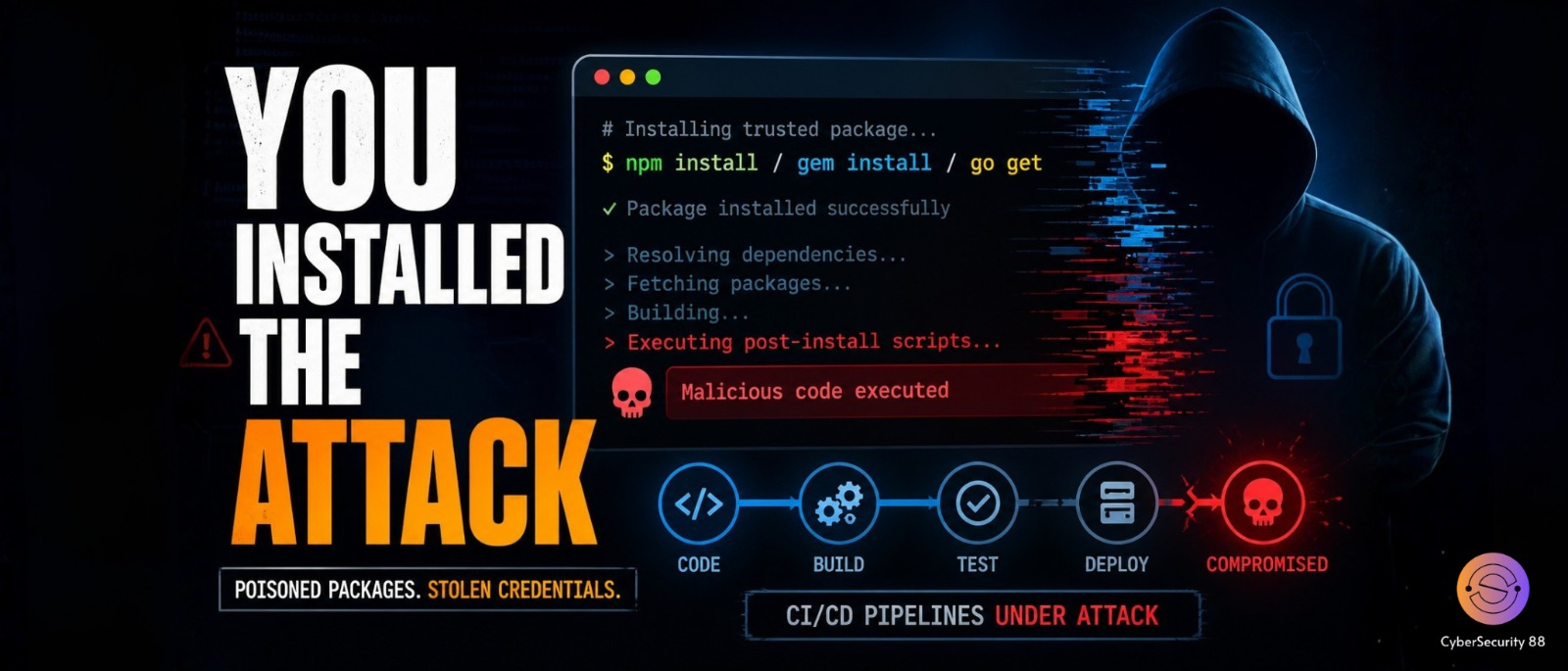
A new cybersecurity threat has been discovered where attackers are using fake open-source packages to target developers and automated systems. These attacks involve malicious Ruby gems and Go modules that were uploaded online and made to look like trusted libraries. The main goal of this campaign is to steal sensitive credentials and gain unauthorized access to systems. It shows how easily developers can be tricked by packages that appear normal. This incident highlights a growing risk in modern software development.

Security researchers found that the attackers created multiple fake packages and hosted them through a GitHub account called BufferZoneCorp. These packages were carefully designed so developers would assume they are safe and useful tools. Once installed, the malicious code runs quietly in the background without obvious signs. This makes it difficult for developers to detect any issue early. The attackers relied on trust rather than force to spread their code.
The attack mainly targets CI/CD pipelines, which are automated systems used to build and deploy applications. These systems often store sensitive data like API keys, tokens, and credentials. By infecting these pipelines, attackers can gain deep access to projects. This allows them to manipulate workflows and potentially control deployments. Because these systems are automated, the attack can spread quickly without manual detection.
One of the most dangerous techniques used in this campaign is called sleeper packages. These packages do not behave maliciously immediately after installation. Instead, they remain inactive for a period of time to avoid detection. After some time, they activate and start executing harmful actions. This delay makes it harder for security tools to identify them early. It gives attackers enough time to stay hidden inside systems.
Several malicious Ruby gems were identified during this campaign. These include knot-activesupport-logger, knot-devise-jwt-helper, knot-rack-session-store, knot-rails-assets-pipeline, and knot-rspec-formatter-json. There were also sleeper gems like knot-date-utils-rb and knot-simple-formatter. These names were chosen to look similar to real libraries. This increases the chances that developers might trust them. Such naming tricks are a common method in supply chain attacks.
The attackers also released malicious Go modules to target another group of developers. These included go-metrics-sdk, go-weather-sdk, go-retryablehttp, go-stdlib-ext, and grpc-client. Just like the Ruby gems, these modules appeared legitimate. Developers could easily confuse them with real and trusted tools. Once installed, they behaved in the same harmful way. This shows that multiple ecosystems were targeted in this campaign.
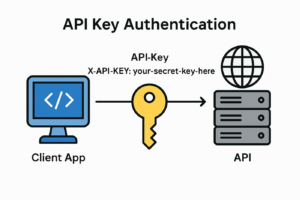
After installation, these malicious packages can perform several dangerous actions. They can steal credentials stored in systems and access tokens used for authentication. They can also modify GitHub Actions workflows and create SSH access for attackers. This allows them to maintain long-term control over compromised systems. The attack does not need direct hacking once access is gained. Everything happens through trusted development tools.
After the discovery, the malicious Ruby gems were removed and the Go modules were blocked. However, systems that already installed them may still be at risk. Security experts say this is part of a larger trend of software supply chain attacks. These attacks focus on poisoning trusted tools instead of breaking into systems directly. It clearly shows the importance of verifying dependencies. Developers must stay cautious because even trusted code can become a threat.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news