A recent cybersecurity report has revealed a serious attack carried out by a North Korea-linked hacking group called ScarCruft. The group targeted a gaming platform and used it to secretly spread malware to users. Instead of attacking people directly, the hackers compromised the platform itself and inserted malicious code into its software. This type of attack is known as a supply chain attack, where even trusted platforms become dangerous without users realizing it. It shows how attackers are now using smarter and indirect methods to reach their targets.

The platform involved in this attack is sqgame.net, which is mainly used by ethnic Koreans living in the Yanbian region of China. This area is geographically sensitive because it is close to North Korea and is often used as a route by defectors. Because of this, experts believe that the attack was not random but highly targeted. The main goal appears to be cyber-espionage and data collection. People like defectors, activists, and researchers were likely the primary targets.
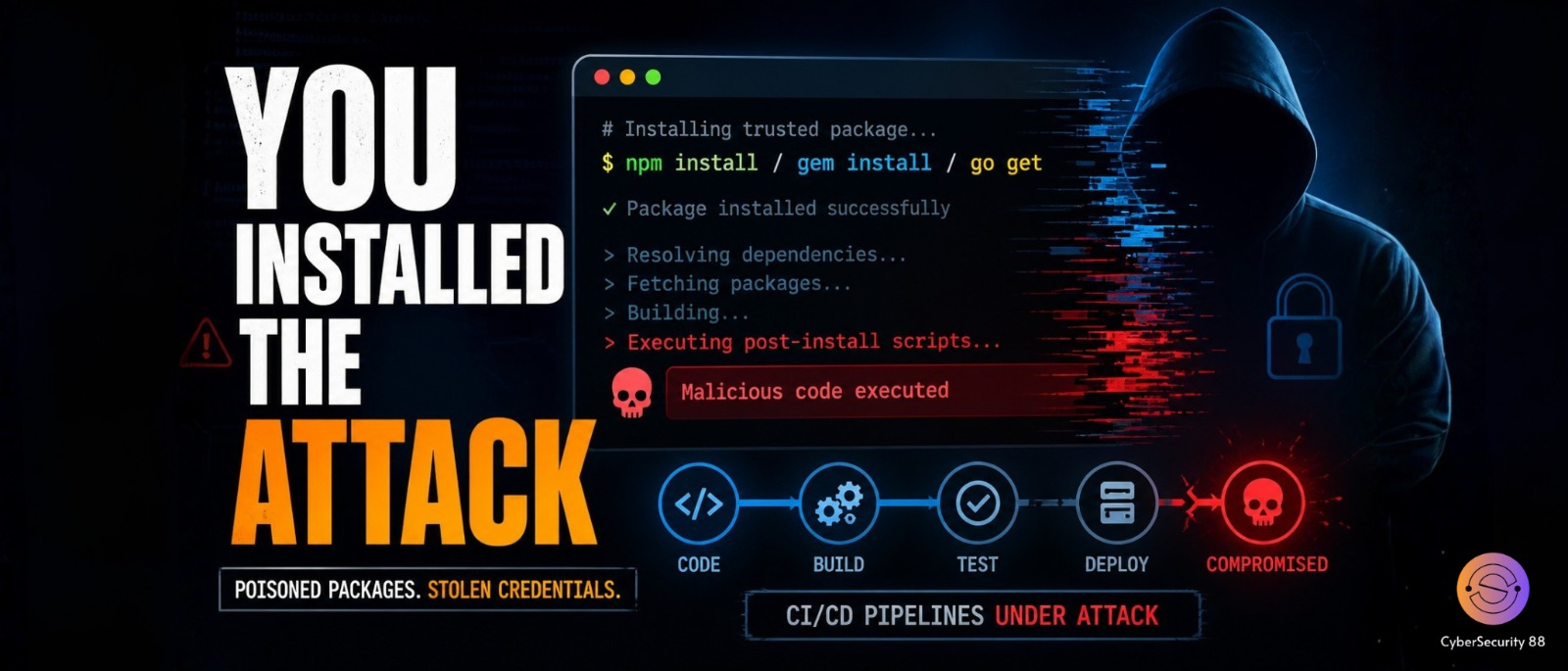
The way the attack was carried out is quite clever and dangerous at the same time. Hackers modified the original game files available on the platform and inserted malware into them. These infected files were then uploaded back to the official website for users to download. So when users downloaded the game, they unknowingly installed malware on their devices. Both Windows and Android versions of the software were affected. This made the attack more widespread and impactful across different types of users.
On Android devices, the attackers modified APK files so that the malware starts running even before the game fully opens. This means users may not even realize something is wrong at the beginning. On Windows systems, the attack follows a slightly different process. A malicious component first installs another malware called RokRAT, which then loads the main threat. This layered method makes detection much harder. It also allows attackers to maintain control for a longer time.
The main malware used in this campaign is called BirdCall, which has been linked to ScarCruft for several years. It is a powerful backdoor that allows hackers to control infected devices remotely. On Windows systems, it can record keystrokes and capture screenshots. It can also steal clipboard data and execute commands from a remote server. This gives attackers deep access to user activity. In simple terms, it can monitor almost everything happening on the system.
On Android devices, the malware is equally dangerous and invasive. It can access contacts, read SMS messages, and collect call logs without permission. It also has the ability to view files like photos and documents stored on the device. In addition, it can record audio and take screenshots silently in the background. The malware also collects device and network information for tracking purposes. This helps attackers build a detailed profile of the victim over time.
One important detail about this malware is how it communicates with the attackers. Instead of using suspicious servers, it relies on trusted cloud services like Dropbox and pCloud. This makes detection much harder because the activity appears normal. Security systems may not flag this communication easily. It allows the malware to stay hidden for a longer period. This is one of the reasons why such attacks are difficult to detect early.
Researchers believe that this campaign has been active since late 2024 and has evolved over time. Multiple versions of the Android malware have already been discovered, showing continuous development. Interestingly, only Android apps were directly infected on download pages, while the Windows client was not always affected in the same way. iOS users were not impacted in this case. This incident clearly shows how advanced cyberattacks have become. It reminds users to stay cautious even when using trusted platforms and downloading normal-looking apps.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news