Search for topics
Trending Searches
Featured Articles

Top 5 Demos from Black Hat USA 2025 That Could Actually Make a Difference
August 07, 2025
Black Hat USA 2025 delivered big this year but only a handful of demos stood out as real game-c...
Read More >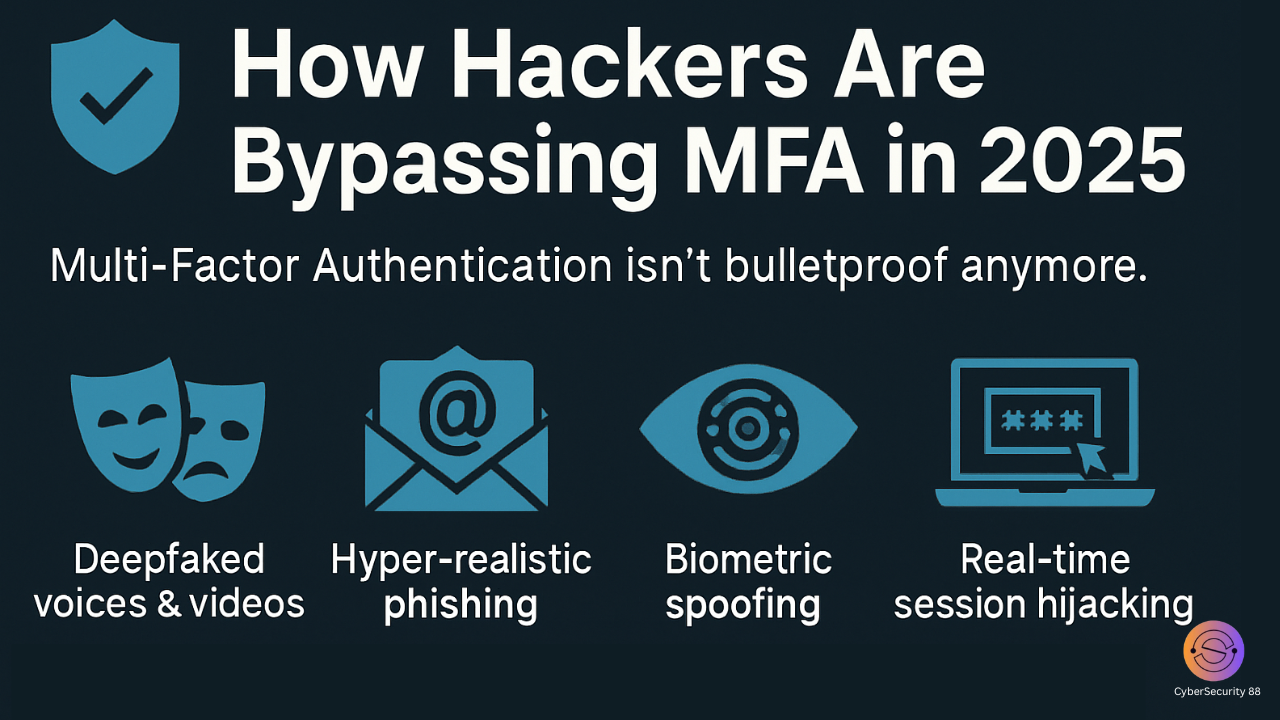
How Hackers Are Bypassing MFA in 2025
August 07, 2025
The Illusion of Security Multi-Factor Authentication (MFA) has long been considered a cornerstone...
Read More >
Malware Detection with LLMs: Hype vs Reality
August 07, 2025
The integration of Large Language Models (LLMs) into malware detection tools has created signific...
Read More >
Inside Supply Chain Attack Techniques: How Hackers Infiltrate
August 07, 2025
Understanding the Threat Landscape At Black Hat USA 2025, one of the most critical sessions unpac...
Read More >
One Click Away from Disaster: Cloud Missteps Exposed
August 07, 2025
Cloud security isn’t failing but misconfigurations are. At Black Hat USA 2025, experts warned t...
Read More >
Ransomware Trends in 2025: What Changed
August 06, 2025
Shift in Target Profiles In 2025, ransomware attacks have escalated in scale and precision. Threa...
Read More >
What the 2025 Black Hat CISO Summit Says About the Future of Cybersecurity
August 06, 2025
The CISO Summit at Black Hat USA is an exclusive, invite-only forum that brings together top cybe...
Read More >

