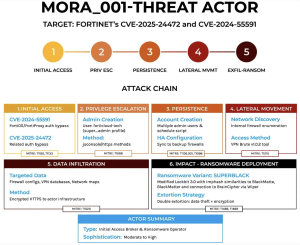
Cybersecurity researchers have uncovered a series of highly sophisticated instructions targeting Fortinet firewall appliances to deploy new ransomware strain “SuperBlack”. This occurred between January and March 2025. The malicious campaign, attributed to a threat actor labeled “Mora_001,” operated throughout Q1 2025, leveraging unpatched security flaws to intrude corporate networks.
Technical Vulnerability Exploitation Chain
Source: Forcescout
The attack begins with the exploitation of two critical vulnerabilities CVE-2024-55591 and CVE-2025-24472 disclosed by Fortinet in January and February. These flaws affect FortiOS versions prior to 7.0.16 and permit unauthorized privilege escalation to super_admin status.
WebSocket vulnerability exploitation via jsconsole interfaces, often masquerading traffic as originating from trusted IPs (127.0.0.1, 8.8.8.8, 1.1.1.1)
Direct HTTPS request manipulation targeting the same underlying security flaw
Forensic evidence indicates that attackers initially probed systems using automated scripts with randomly generated fice-character usernames before establishing persistent access through carefully crafted admin accounts.
The threat actor employed multiple multiple persistence layers to maintain access.:
There have evidence of FortiGate automation scripts configured to regenerate compromised admin accounts at predetermined intervals using system.automation-action function.
In environments with redundant firewall configurations, the attackers triggered HA synchronization to get theri backdoor credentials across multiple devices.
The group attempted to exploit TACACS+ and RADIUS authentication systems to expand their persistence and lateral movement using VPN credentials and newly added VPN accounts.
Mora_001 exfiltrates data using a custom tool before encrypting files for double extortion, focusing primarily on file and database servers, as well as domain controllers.
After encryption, ransom notes are left on the victim’s system. A custom-built wiper, named ‘WipeBlack,’ is then deployed to erase all traces of the ransomware executable, tampering evidence.
LockBit and SuperBlack
The “SuperBlack” ransomware exhibits significant code similarities with the LockBit 3.0 malware family.
Technical analysis of the encryption executable revealed:
- Import hash 914685b69f2ac2ff61b6b0f1883a054d, previously associated with BlackMatter and LockBit variants.
- Advanced anti-forensic capabilities, including dynamic Windows API resolution to prevent static analysis
- A modular structure featuring a primary encryption payload and a secondary “WipeBlack” component.
- Interprocess communication are named pipes, with encrypted command sequences using XOR key 0x3105DFDE.
- Self-deletion mechanisms that overwrites the ransomware executable.
This campaign employed sophisticated attack infrastructure with multiple proxy layers and specialized brute-force tools. Security researchers found at least 15 IP addresses hosting a Russian-language utility called “VPN Brute,” designed to target edge security devices.
This tool supports:
- Multi-threading credential attacks against various VPN technologies
- Proxy rotation to avoid IP-based blocking
- Honeypot detection capabilities to evade security researchers
- Specialized modules for RDWeb, PulseSecure, OWA, GlobalProtect, Fortinet, Cisco, BIG-IP, and Citrix platforms
The tool’s SSH fingerprint (fa3f3f12cee3c18aa50ea8b8e38708cad06875e617164baca8f8ee7156459249) has been flagged as an indicator of compromise in multiple security incidents.
The Bottom Line
Vulnerability scans reveal substantial exposure of unpatched Fortinet appliances globally, but the appliances, exposed management interfaces face particularly high risk, as these interfaces provide direct access to the vulnerable components exploited in these attacks.
Source:hxxps[://]www[.]forescout[.]com/blog/new-ransomware-operator-exploits-fortinet-vulnerability-duo/
Follow us on X and Linkedin for the latest cybersecurity news.