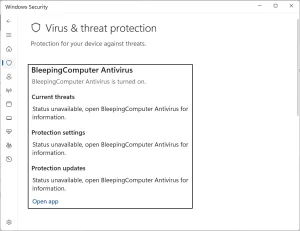
A newly released tool named Defendnot can effectively disable Microsoft Defender on Windows systems by exploiting an undocumented Windows Security Center (WSC) API. Developed as a security research project by researcher es3n1n, the tool tricks Windows into believing a legitimate antivirus solution is installed, even when no actual security software is present.
Under normal conditions, Microsoft Defender automatically deactivates itself when another antivirus program registers with the Windows Security Center to avoid software conflicts. Defendnot exploits this behavior by registering a fake antivirus product that passes all WSC validation checks, effectively fooling the system into shutting down Defender.
The technique builds upon an earlier project, no-defender, which used components from a third-party antivirus solution to spoof WSC registration. That project was eventually removed from GitHub after the antivirus vendor filed a DMCA takedown. In contrast, Defendnot circumvents legal and copyright issues by creating its own dummy antivirus DLL from scratch.
To bypass built-in security mechanisms such as Protected Process Light (PPL) and digital signature verification, Defendnot injects its DLL into Taskmgr.exe, a trusted and Microsoft-signed system process. From within this process, it registers the fake antivirus software under a spoofed name, prompting Defender to disable itself immediately.
The tool includes a loader component that uses a configuration file, ctx.bin, to customize its behavior. Users can set the spoofed antivirus name, toggle registration on or off, and enable verbose logging for debugging or monitoring.
For persistence, Defendnot creates a scheduled task that ensures it runs at every user login, keeping Defender disabled unless manually reversed.
While Defendnot is intended as a proof-of-concept for research purposes, it highlights a significant vulnerability in how Windows handles antivirus registration. Microsoft Defender currently flags the tool as Win32/Sabsik.FL.!ml, quarantining it upon detection.
The release underscores how trusted system features, when improperly secured, can be manipulated to disable core security protections, raising concerns for both enterprise and consumer users alike.
For More Info: https://github.com/es3n1n/defendnot
Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news







