A new wave of deceptive websites mimicking as the Google Play Store has emerged, distributing SpyNote, a notorious Android malware. These malicious sites are hosted on newly registered domains and designed to trick visitors into downloading infected applications by mimicking legitimate Play Store pages.

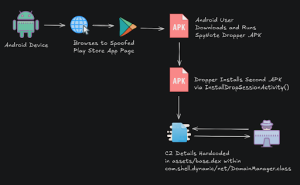
Attack Chain
According to researchers, these sites employ a clean user interface, including an image carousel showcasing fake screenshots. These visuals, intended to create the illusion of authenticity, are loaded from the suspicious domain “bafanglaicai888[.]top,” which is believed to be controlled by the same threat actor.
A HTML element manages the interface’s functionality, including the deceptive “Install” button that triggers the download of the malware-laden .apk file through a JavaScript function named download().
The malicious application delivered through this method is SpyNote, a powerful Remote Access Trojan (RAT) capable of surveillance, data theft, and full remote control over infected devices.
The malicious .apk file acts as a dropper, containing and installing a second-stage payload via a function named InstallDropSessionActivity(). This function implements DialogInterface.OnClickListener, which activates upon user interaction—likely when a “Confirm” button is clicked in a deceptive user dialog labeled “User Data Info.”
Attribution
Technical analysis of the dropped .apk files confirms the presence of SpyNote, and in some cases, its variant SpyMax. These RATs are known for their use by advanced persistent threat (APT) groups such as OilRig (APT34), APT-C-37 (Pat-Bear), and OilAlpha, and have previously used in targeted campaigns against Indian defense personnel.
What sets this campaign different is the incorporation of both English and Chinese-language elements. The delivery sites include Chinese-language comments in the HTML code, suggesting links to Chinese-speaking threat actors or operations targeting Chinese-speaking users. This bilingual approach may be part of an effort to widen the attack’s reach or hide its origins.
The Bottom Line
SpyNote’s popularity among both sophisticated APT groups and low-level cybercriminals is largely due to the availability of builder tools in underground forums. These tools make it easier to customize and deploy the malware, contributing to its continued proliferation in mobile cybercrime and espionage campaigns.
Source: hxxps[://]dti[.]domaintools[.]com/newly-registered-domains-distributing-spynote-malware/
Follow us on X and Linkedin for the latest cybersecurity news







