The Cybersecurity and Infrastructure Security Agency (CISA) has confirmed that a serious vulnerability in FileZen is being actively exploited. The flaw is tracked as CVE-2026-25108. Because of confirmed attacks, CISA added it to its Known Exploited Vulnerabilities catalog. This means the threat is real and organizations must act quickly.

FileZen is a secure file transfer product developed by Soliton Systems K.K.. It is widely used by organizations to safely send and receive sensitive files. A security weakness in such software can create major risks. That is why this issue is being treated with high priority.
The vulnerability is classified as an OS command injection flaw. In simple terms, it allows an attacker to send specially crafted input that the system may treat as a command. If successful, the server could execute unauthorized operating system commands. This can potentially give attackers control over the affected system.
The issue becomes exploitable only when the “Antivirus Check Option” feature is enabled in FileZen. An attacker must also have access to a valid account on the web interface. Even a low-privilege user account may be enough under these conditions. This makes internal access control extremely important.
According to official advisories, the affected versions include V4.2.1 through V4.2.8 and V5.0.0 through V5.0.10. Both physical and virtual editions in these ranges are impacted. However, FileZen S is not affected by this vulnerability. Organizations should carefully verify which version they are running.
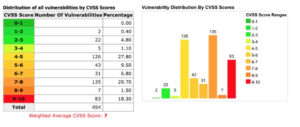
Security scoring systems rate this flaw as high severity. The CVSS score is reported to be around 8.7 to 8.8 out of 10. This indicates a serious level of risk if exploited successfully. The combination of active exploitation and high severity increases urgency.
To address the problem, the vendor has released FileZen version V5.0.11. This updated version fixes the vulnerability completely. Users running older affected versions are strongly advised to upgrade immediately. Updating is the primary and most effective mitigation step.
CISA has emphasized that organizations should not delay remediation. Agencies that follow federal cybersecurity directives must patch within the required deadline. Administrators are also encouraged to review logs and monitor for suspicious activity. This incident highlights how quickly vulnerabilities can turn into real-world attacks if not addressed promptly.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news