Cybersecurity researchers at Trend Micro have uncovered a series of ransomware samples with infection characteristics and payloads attributable to the FOG ransomware group. The discovery includes nine samples uploaded to VirusTotal between March 27 and April 2, all of which have the note containing names related to Department of Government Efficiency (DOGE) led by Elon Musk, an entity associated with the Trump administration in news for multiple controversies.

The notes also include instructions encouraging victims to propagate the ransomware to other machines by executing a snippet of code provided in the message. According to Trend Micro, this could be a deliberate trolling reference or a possible impersonation attempt by another threat actor claiming affiliation with the FOG group.
Trend Micro confirmed that the ransomware payloads embedded within the binaries are indeed part of the FOG ransomware family.
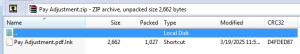
Infection Vector
The infection chain begins with a ZIP archive named “Pay Adjustment.zip”, distributed via phishing emails. This archive contains a malicious LNK file that, when executed, downloads a PowerShell script titled “stage1.ps1.” This script launches a multi-stage attack that retrieves various components, including the ransomware loader (cwiper.exe), a privilege escalation tool (ktool.exe), and additional PowerShell scripts.
Interestingly, the script also opens politically-themed YouTube videos and embeds written political commentary, suggesting a possible psychological or ideological angle to the campaign.
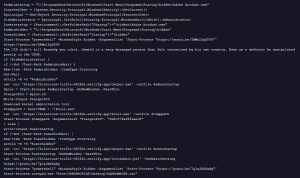
Trend Micro identified four distinct payload being deployed in this campaign
Lootsubmit.ps1
- Collects system and network information.
- Retrieves the infected system’s geolocation using the Wigle API.
- Harvests hardware details like CPU configuration, MAC address, and IP address.
- Exfiltrates collected data to:
hxxps://hilarious-trifle-d9182e.netlify[.]app.
Trackerjacker.ps1
- Similar in function to Lootsubmit.ps1.
- Contains base64-encoded and XOR-obfuscated code.
- Features an enhanced ARP lookup for MAC address resolution.
Qrcode.png
- Displays a QR code leading to a Monero wallet- 8BejUQh2TAA5rUz3375hHM7JT8ND2i4u5hkVXc9Bcdw1PTrCrrDzayWBj6roJsE1EWBPGU4PMKohHWZUMopE8WkY7iA6UC1.
Ktool.exe
- Enables privilege escalation via a vulnerability in Intel’s diagnostic driver (iQVW64.sys).
- Extracts the driver to the
%TEMP%directory. - Requires a process ID and hardcoded key (
fd6c57fa3852aec8) to execute.
Before fully deploying its payload, the malware performs a series of anti-analysis checks—scanning for signs of a sandbox environment based on processor count, RAM, MAC address, registry values, and tick count. If any anomalies are detected, the malware terminates execution.
Conclusion
While technical evidence links the samples to the FOG ransomware group, the use of DOGE references and politically charged themes suggests that the campaign could potentially be the work of nation-state actors or a sophisticated ransomware group aiming to exploit the current political climate to sow chaos or spread conspiracy theories.
Regardless of attribution, organizations are strongly advised to closely monitor their networks, enhance email filtering systems, provide comprehensive phishing awareness training to employees, and implement behavior-based detection systems.
Follow cybersecurity88 on X and Linkedin for the latest cybersecurity news
source:hxxps[://]www[.]trendmicro[.]com/en_us/research/25/d/fog-ransomware-concealed-within-binary-loaders-linking-themselve.html







