ReversingLabs has identified a malicious open-source package on PyPI masquerading as a legitimate tool for Solana blockchain development. The package, named solana-token, appeared to be a utility for developers but was designed to exfiltrate source code from a developer’s machine upon installation.
Although the package’s PyPI landing page lacked a description, its name and functions were crafted to appeal to developers working on blockchain applications. This strongly suggests that the attackers aimed to target individuals building custom blockchain solutions.
Before PyPI removed solana-token, it had been downloaded more than 600 times—potentially as a result of links shared on developer-focused platforms.
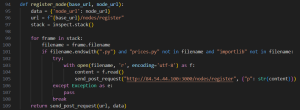
The ReversingLabs research team found that the package’s behavior focused on two main goals: stealing application source code and collecting sensitive data or secrets embedded within it. One method in the package, which ostensibly implemented blockchain functionality, instead scanned the Python execution stack and exfiltrated source code files to a remote server.
This type of behavior is unusual compared to other malicious open-source packages previously discovered by ReversingLabs. Researchers believe the attackers were attempting to harvest hardcoded crypto-related secrets, which are often left exposed in source code. Such secrets could be used to compromise critical infrastructure, including access to cryptocurrency wallets and blockchain applications.
This incident comes just a week after another high-impact supply chain attack was discovered in the npm ecosystem. A package named “rand-user-agent@1.0.110“, which received roughly 45,000 weekly downloads, was found to contain malicious code capable of enabling remote access and exfiltrating user data. The scale and reach of that attack caused even greater disruption, highlighting the increasing sophistication and ambition of threat actors targeting open-source software repositories.
Cybersecurity experts urges developers to audit any projects that may have included the solana-token package and to rotate credentials that may have been exposed. Developers are also encouraged to adopt stricter hygiene practices, such as using environment variables for secrets and verifying third-party packages before use.
Source: hxxps[://]www[.]reversinglabs[.]com/blog/same-name-different-hack-pypi-package-targets-solana-developers
IOC
- f4e1149360174b4fcf0dcc6e61898c8180324893
- 0b8697f8e81956e7c0c5383806fa69630c38ad33
- 07457e36bf9aab1dc2b54acd30ec8f9e5c60c84
- 9719d1e076ab67a18f231889cad4b451f539ce7
Follow Cybersecurity88 on X and Linkedin for the latest cybersecurity news








