A malicious software package pretending to be a Stripe integration library was recently discovered on the NuGet repository. The fake package was created to closely imitate Stripe’s official .NET library used for payment processing. At first glance, it looked legitimate and worked like the real tool. However, hidden inside it was code designed to steal sensitive API tokens.

The malicious package was named StripeApi.Net, which closely resembled the official Stripe.net library. Attackers copied the original package’s icon and description to make it appear authentic. This tactic is known as typosquatting, where small name differences are used to trick developers. Because many developers install dependencies quickly, such subtle changes can easily be missed.
The package was uploaded to NuGet in mid-February 2026 under the publisher name “StripePayments.” Before it was removed, it had accumulated more than 180,000 downloads. The high download count made it look trusted and widely used. In reality, it was silently collecting sensitive information from users.
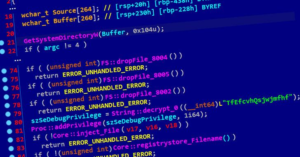
Despite being malicious, the package allowed normal Stripe payment operations to continue. This made it difficult for developers to notice anything suspicious. Behind the scenes, the hidden code extracted Stripe API tokens. These tokens were then sent to a remote server controlled by the attackers.
Stripe API tokens provide access to payment accounts and transaction capabilities. If stolen, they could allow unauthorized access to financial operations. This makes the compromise particularly serious for businesses relying on Stripe services. Even though no confirmed misuse has been reported, the risk was significant.
The threat was discovered by researchers at ReversingLabs, a company focused on software supply chain security. After detection, the package was reported and removed from the NuGet repository. Early investigations have not confirmed any confirmed cases of stolen tokens being abused. However, the incident highlights weaknesses in open-source ecosystems.
In recent years, many malicious NuGet packages have targeted cryptocurrency-related tools. This case is different because it focused on a widely used financial integration library. It shows that attackers are expanding beyond crypto and targeting mainstream software services. The strategy reflects a shift toward broader financial and enterprise-focused attacks.
This incident serves as an important reminder for developers and organizations. Even trusted repositories like NuGet can host malicious packages. Verifying publishers, reviewing package details, and scanning dependencies are critical security steps. As reliance on third-party libraries increases, software supply chain security becomes more essential than ever.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news