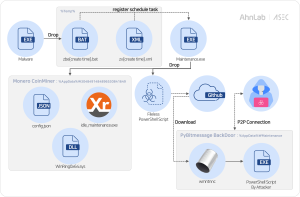
The AhnLab Security Intelligence Center (ASEC) has discovered a new backdoor malware strain bundled with a Monero cryptocurrency miner. Unlike other malware that uses HTTP or IP-based communication, this malware uses PyBitmessage library to communicate over a peer-to-peer (P2P) network, encrypting its traffic between endpoints.
What is PyBitmessage?
Bitmessage is a protocol designed for anonymity and decentralization, preventing interception and masking both sender and receiver identities. The attackers exploit PyBitmessage, a Python-based implementation of this protocol, to exchange encrypted packets disguised as regular network traffic to evade detection.
Attack Chain
The Monero miner and backdoor are embedded in the top-level executable’s resources and encrypted using XOR. Upon execution, the malware decrypts these components and stores three key files
config.jsonWinRing0x64.sysidle_maintenance.exe
in the %Temp%\3048491484896530841649 directory.
Monero is commonly used in such attacks due to its strong privacy features, allowing attackers to profit anonymously by hijacking system resources for mining.
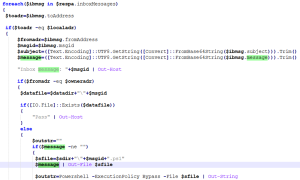
Upon launch, the PowerShell-based backdoor installs PyBitmessage to handle POST requests via localhost port 8442. It attempts to download PyBitmessage from its GitHub release page, or from a Russian-based file hosting service likely linked to the attacker.
The PyBitmessage package, bundled via PyInstaller, creates .pyc, .pyd, and related module files in the %TEMP%\_MEI~~ directory upon execution.
Among them is QtGui4.dll, which appears to be patched (with a specific offset zeroed out) to disable its standard functionality, potentially as an evasion technique.
After setup, the malware initializes multiple files and directories needed for operation and waits for further instructions from the attacker. These instructions are delivered as encrypted messages, saved locally, and executed as PowerShell scripts from a hidden path (.\s).
The Bottom Line
Evidence points to Russian or Russian-speaking threat actors based on backup file hosting site’s Russian language interface and geographic hosting location. This malware demonstrates how cybercriminals are weaponizing legitimate privacy tools, creating detection challenges that require fundamental shifts in security monitoring approaches from traditional signature-based to behavioral analysis methods.
Source: hxxps[://]asec[.]ahnlab[.]com/en/88109/
Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news