The National Institute of Standards and Technology (NIST) has made an important change in how it manages cybersecurity vulnerabilities. This decision comes after a huge increase in the number of reported vulnerabilities in recent years. Because of this growth, NIST will now limit the detailed analysis, also called enrichment, that it adds to CVEs. Earlier, most vulnerabilities received full analysis, but that is no longer possible at this scale. The change is mainly focused on managing workload and maintaining efficiency.

The biggest reason behind this move is the sharp rise in CVE submissions over the past few years. NIST reported that vulnerability submissions have increased by 263% between 2020 and 2025. This trend is still continuing in 2026, with numbers already higher than the previous year. Even though NIST enriched around 42,000 CVEs in 2025, the number of new entries is growing faster. This imbalance has made it difficult to maintain detailed analysis for every vulnerability.
Under the updated system, all vulnerabilities will still be listed in the National Vulnerability Database (NVD). However, not every CVE will receive detailed enrichment like before. Some entries will be published with basic information and marked as “Not Scheduled.” This means they will not be prioritized for further analysis by NIST. Users will still be able to view these vulnerabilities, but with limited details available.
NIST has also explained which types of vulnerabilities will be given priority moving forward. These include CVEs that are part of the Known Exploited Vulnerabilities catalog maintained by CISA. It will also focus on vulnerabilities affecting software used by the federal government. In addition, high-impact vulnerabilities involving critical systems or elevated privileges will be prioritized. These categories are considered the most serious and require immediate attention.
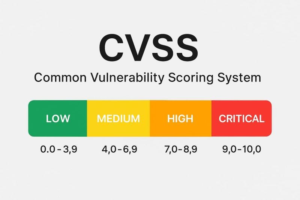
Another change is related to how severity scoring will be handled in the future. NIST will no longer provide its own severity score if one has already been assigned by the reporting organization. This helps avoid duplicate work and reduces unnecessary effort. Also, if a vulnerability is updated later, it will only be reanalyzed if the change significantly affects the original data. This ensures better use of time and resources.
This decision is also connected to the growing backlog of vulnerabilities in recent years. NIST has faced increasing difficulty in keeping up with the rising number of reports. The use of automated tools and AI has made vulnerability discovery much faster. While this improves detection, it also increases the pressure on systems like the NVD. Managing every vulnerability in detail has become practically impossible.
To handle this situation, NIST is shifting toward a risk-based prioritization approach. This means focusing more on vulnerabilities that pose the highest risk to systems and organizations. Instead of analyzing everything equally, attention will be given to the most critical threats. This approach is expected to improve efficiency and maintain the quality of important data. NIST is also working on improving automation and internal processes.
Overall, this change highlights a major challenge in today’s cybersecurity landscape. The number of vulnerabilities is growing faster than organizations can manage. While the new approach helps NIST focus on critical issues, it also means some vulnerabilities may not get detailed analysis. Organizations relying on this data may need to adjust their strategies. It clearly shows the need for better prioritization in modern cybersecurity.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news