FortinGuard Labs issued an advisory for CVE-2025-32756, a critical vulnerability affecting multiple Fortinet products. Just a day later, CVE-2025-32756 was added to CISA’s Known Exploited Vulnerabilities (KEV) catalog. Today researchers at Horizon3.ai released a proof-of-concept (PoC) demonstrating exploitation of the vulnerability. Their analysis focused on comparing the patched and unpatched versions of FortiMail.

CVE-2025-32756
According to the advisory, CVE-2025-32756 is a stack-based buffer overflow within the administrative API that allows unauthenticated remote code execution. The vulnerability stems from improper handling of user-supplied data in the AuthHash field of a cookie named APSCOOKIE.
Proof-of-concept (PoC) for CVE-2025-32756
Horizon3.ai started their research using the IOC provided in the advisory and confirmed admin.fe CGI binary is the exploitation target.
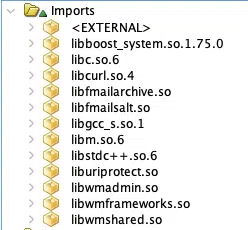
While the admin.fe binary remained identical across both versions, further investigation revealed that the issue resides in a shared library: libhttputil.so. A significant clue was the presence of cookie fields (Era, Payload, AuthHash) found only in this library.
Using tools like Ghidra, Horizon3.ai tracked the vulnerability to a function named cookieval_unwrap(), which decodes base64-encoded fields. The unpatched version lacks bounds checking for the decoded size of AuthHash, leading to a classic buffer overflow. The patched version introduces a check to ensure the input length is below a safe threshold (less than 30 bytes).
The overflow allows overwriting several stack variables, including saved registers and the return address. This enables precise control over program execution. By supplying a crafted base64-encoded string, the researchers were able to trigger the overflow and hijack execution.
Notably, the web server configuration and its use of mod_fcgid make this vulnerability easier to exploit reliably, as failed attempts are less likely to crash the application.
Conclusion
While Horizon3.ai did not publish a full exploit, their findings highlight the high exploitability of CVE-2025-32756 and underscore the urgent need to patch.
Given the nature of the vulnerability and the availability of a PoC, organizations using affected Fortinet products should update immediately and monitor for signs of compromise.
Source: hxxps[://]horizon3[.]ai/attack-research/attack-blogs/cve-2025-32756-low-rise-jeans-are-back-and-so-are-buffer-overflows/







