FortiGuard Labs has identified a new botnet, dubbed “RustoBot,” actively exploiting vulnerabilities in TOTOLINK devices. Notably, this variant is written in Rust—a modern, secure programming language.
Spike in TOTOLINK Exploits
Between January and February 2025, FortiGuard observed a surge in cyberattacks exploiting known vulnerabilities in TOTOLINK networking hardware. These attacks are based on the cstecgi.cgi script, a core component responsible for handling configuration and administrative functions.
This script has long been plagued by remote command injection flaws—particularly CVE-2022-26210 (setUpgradeFW) and CVE-2022-26187(pingCheck)—which allow attackers to execute arbitrary code.
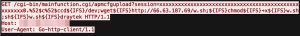
During analysis, researchers identified signs of larger attack campaigns. One payload, hosted at hxxp://66[.]63[.]187[.]69/mpsl, revealed exploitation of CVE-2024-12987—a vulnerability in DrayTek devices that allows OS command injection through the cgi-bin/mainfunction.cgi/apmcfgupload interface.
These exploits were traced across four countries—Japan, Taiwan, Vietnam, and Mexico.
Deepdive into RustoBot
“RustoBot” has been observed targeting multiple device architectures, including arm5, arm6, arm7, mips, and mpsl, with an additional x86 variant also discovered. The malware predominantly focuses on TOTOLINK devices, especially those using the mpsl architecture.
What sets RustoBot apart is its Rust-based implementation. Upon execution, the malware retrieves system API functions from the Global Offset Table (GOT) and performs a series of obfuscated operations, including the use of xor, shr, and rol instructions, to decode its configuration. XOR-based encryption is employed to hide its core logic and functionality from static analysis.

Once operational, RustoBot performs two main malicious actions:
- Command and Control (C2) Communication – It resolves four suspicious domains (
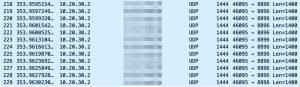
dvrhelper[.]anondns[.]net,techsupport[.]anondns[.]net,rustbot[.]anondns[.]net, andmiraisucks[.]anondns[.]net) via DNS-over-HTTPS (DoH) to evade detection by blending into regular HTTPS traffic. These domains all point to the same IP address:5[.]255[.]125[.]150. - DDoS Attacks – After retrieving configuration data from the C2 server, RustoBot launches UDP-based distributed denial-of-service (DDoS) attacks. Key parameters include the victim’s IP, port numbers, attack duration (30 seconds), and packet size (1400 bytes).
Conclusion
The emergence of RustoBot underscores the ongoing threat posed by inadequately secured IoT and network devices. With malware authors leveraging advanced languages like Rust to enhance obfuscation and performance, defenders face new challenges in detection and mitigation. Experts recommends strengthening device authentication, improving endpoint security, and ensuring timely firmware updates as essential measures to prevent RustoBot.
Follow cybersecurity88 on X and Linkedin for the latest cybersecurity news
Source:hxxps[://]www[.]fortinet[.]com/blog/threat-research/new-rust-botnet-rustobot-is-routed-via-routers








