A recently uncovered web skimming campaign is using a legacy Stripe API to validate stolen payment details before exfiltration, reducing the chances of detection. Researchers from Jscarambler identified at least 49 compromised merchants, with numbers expected to rise as more victims are uncovered.
How the Attack Operates
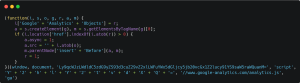
The attack employs multiple stages to load skimming logic on checkout pages. Initially, threat actors inject a malicious loader script, often disguised as a Google Analytics variant, by exploiting vulnerabilities in WordPress and WooCommerce.
Then a base64-encoded code string is decoded to load skimmer. The skimmer script overlays the legitimate Stripe payment iframe with a fake one to capture card details. If the data is legit, it is sent to a server controlled by attackers, while users are forced to reload the page.

Researchers also observed that also target other payment platforms, including Square. Attackers sometimes introduce alternative payment options, such as cryptocurrency payments via fake MetaMask wallet pop-ups.
Since the skimming process mimics legitimate API calls, it evades traditional detection methods. Attackers exploit deprecated API versions, which may eventually aid in identifying fraudulent activity.
Conclusion
The team identified over 20 related domains, hinting at a larger and sophisticated campaign. Despite efforts to alert affected merchants, only 15 have successfully removed the malicious scripts.Merchants are urged to update their security protocols to safeguard against similar threats.
Source: hxxps[://]jscrambler[.]com/blog/stripe-api-skimming-campaign
Follow us on X and Linkedin for the latest cybersecurity news
Related Reading
1.Buyer’s Guide to Payment Gateways: Pros, Cons, and Key Considerations







