A newly discovered Windows vulnerability, tracked as CVE-2025-24054, is being actively exploited in the wild, prompting urgent warnings from security researchers. This flaw allows attackers to leak NTLMv2-SSP hashes using .library-ms files, exposing users to credential theft, lateral movement, and full domain compromise.
Though it was fixed by Microsoft on March 11,2025, threat actors began exploiting CVE-2025-24054 as early as March 19, as many of the devices had not been patched quickly.
Background on NTLM
NTLM (New Technology LAN Manager) is Microsoft’s legacy authentication protocol, now widely recognized as outdated and vulnerable. Though NTLMv2 improved security over NTLMv1, it still allows for hash relay and brute-force attacks if the response (Net-NTLMv2 hash) is captured.
If the leaked credentials belong to privileged accounts—and if defenses like SMB signing and NTLM relay protectionare missing—the attacker could gain domain-level access.
CVE-2025-24054 Actively Exploited in the Wild
CVE-2025-24054 is a NTLM hash disclosure vulnerability triggered through a crafted .library-ms file. When such a file is extracted or even minimally interacted with—such as right-clicking or navigating to its folder—Windows Explorer initiates an SMB authentication request to a remote attacker-controlled server, thereby leaking the user’s NTLMv2 hash.
This behavior mirrors that of CVE-2024-43451, a similar spoofing vulnerability patched last November and previously exploited in Ukraine by Russian-linked group UAC-0194.
Attack Chain
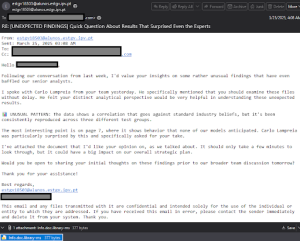
Researchers from CheckPoint Research found that within 8 days of patching, malicious campaigns began exploiting CVE-2025-24054. A prominent wave—dubbed the “NTLM Exploits Bomb Campaign“—was observed on March 20–21, targeting government and private entities in Poland and Romania.

Victims were lured via malspam emails containing Dropbox links to archives like xd.zip. These contained four files designed to provoke NTLM hash leaks:
xd.library-ms— exploited CVE-2025-24054 with no user interaction required.xd.url— abused CVE-2024-43451 by initiating SMB connections via UNC paths.xd.website— a more modern shortcut type, also triggering SMB connections.xd.lnk— traditional Windows shortcuts initiating manual SMB connections.
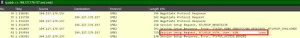
All the files are attempted to connect to the malicious server at 159.196.128[.]120, linked to APT28 (Fancy Bear), although no direct attribution has yet been made. There have also been several instances where the .library-ms file was shared via email without being zipped.
Mitigation
CVE-2025-24054 was originally tracked as CVE-2025-24071 before reclassification. Microsoft issued a patch on March 11, but the rapid exploitation suggests many systems remain vulnerable.
Security experts recommend
- Immediate application of the March 2025 Patch Tuesday updates
- Disabling NTLM authentication where possible
- Enabling SMB signing and Extended Protection for Authentication (EPA)
- Deploying monitoring solutions to detect outbound SMB connections to unknown IPs
Follow us on X and Linkedin for the latest cybersecurity news
Source:hxxps[://]research[.]checkpoint[.]com/2025/cve-2025-24054-ntlm-exploit-in-the-wild/







