A severe security flaw in the popular Alone – Charity Multipurpose Non-profit WordPress Theme is currently being exploited by malicious actors to compromise WordPress sites through unauthorized plugin installations.
Identified as CVE-2025-5394 and rated 9.8 on the CVSS scale, the flaw was discovered by security researcher Thái An. It impacts all theme versions up to 7.8.3 and has been patched in version 7.8.5, released on June 16, 2025.
According to Wordfence, the issue lies within the alone_import_pack_install_plugin() function, which fails to verify user capabilities. This oversight allows unauthenticated users to trigger remote plugin installations via AJAX, opening the door to arbitrary file uploads and remote code execution (RCE).
“This vulnerability lets attackers upload and execute arbitrary files without authentication—resulting in full control over the affected site,” said István Márton from Wordfence.
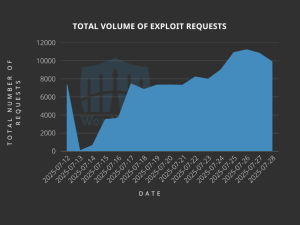
Attack attempts have been tracked back to July 12, suggesting the attackers may have been monitoring theme updates to exploit vulnerabilities before public disclosure.
To date, over 120,000 exploit attempts have been blocked, with activity traced to several IP addresses, including:
In these attacks, hackers often upload ZIP files (like wp-classic-editor.zip or background-image-cropper.zip) containing PHP-based backdoors. These allow remote command execution, upload of malicious files, and creation of rogue admin accounts using stealthy file managers.
Recommended Actions:
Website administrators using this theme should immediately update to the latest version, investigate any suspicious admin accounts, and review logs for signs of exploitation—particularly requests to:/wp-admin/admin-ajax.php?action=alone_import_pack_install_plugin.
Stay alert, and keep your security measures updated!
Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news