A new cybercrime campaign has been discovered where attackers are using fake CAPTCHA pages to trick people into sending costly SMS messages without realizing it. At the same time, researchers have identified more than 120 large-scale campaigns powered by Keitaro, which are spreading cryptocurrency scams and malware globally. This combination shows how cybercriminals are blending simple social engineering with advanced tools. The scale of this operation makes it a serious global threat. It also highlights how everyday internet actions can be manipulated for fraud.
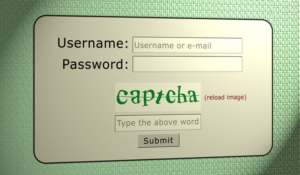
The fake CAPTCHA scam works in a very deceptive way and looks completely legitimate at first glance. Users are shown a familiar “I am not a robot” style verification page. Instead of verifying anything, the page asks users to send an SMS message to confirm they are human. Once the user follows the instructions, multiple SMS messages are triggered automatically. In some cases, victims may unknowingly send 50 to 60 messages. This results in unexpected charges that only appear later on their phone bills.
This attack is based on a fraud model known as International Revenue Share Fraud, which is widely used in telecom scams. In this method, attackers use premium international phone numbers that generate revenue for each message received. Telecom operators charge users for sending these messages. A part of that money is then shared with the fraudsters behind the scheme. This allows attackers to earn profit directly from user interaction. The more messages sent, the higher the earnings for the criminals.
Researchers found that the attackers used multiple premium-rate numbers across different countries to run this operation. These numbers are carefully chosen from regions where regulations may be weaker or charges are higher. This increases the profit margin for the attackers. Because the messages are sent internationally, the costs per SMS are significantly higher than normal. Victims often do not notice anything unusual during the process. The financial impact only becomes clear when the phone bill arrives.
The attackers also used several advanced techniques to make the scam harder to escape and detect. One key method is back button hijacking, where pressing the back button simply reloads the same malicious page. This traps users and keeps them engaged with the scam. They also use multi-step CAPTCHA flows, where each step triggers additional SMS messages. Cookie tracking is used to monitor user actions and guide the attack process. Traffic is redirected through hidden chains, making detection by security systems more difficult.
Alongside the SMS scam, the use of Keitaro plays a major role in scaling these attacks globally. Keitaro is normally a marketing tool used to manage and distribute web traffic. However, in this case, it has been misused to run over 120 malicious campaigns. These campaigns were active between October 2025 and January 2026. They were used to deliver malware, fake investment platforms, and phishing pages. This shows how legitimate tools can be turned into powerful cybercrime systems.
A major portion of these campaigns focused on cryptocurrency-related fraud, which has become increasingly common. Around 96% of the spam traffic linked to these campaigns promoted crypto scams. These included fake airdrops, wallet-draining attacks, and fake AI trading platforms promising high returns. Attackers also used deepfake videos of celebrities to build trust and attract victims. Many users fall for these scams due to the realistic appearance of the content. This makes the campaigns highly effective and dangerous.
Overall, this entire operation is harmful because it targets users in multiple ways at the same time. Victims can lose money through hidden SMS charges as well as crypto-related fraud. Another issue is that these charges are delayed, making detection more difficult. The campaign shows how even trusted elements like CAPTCHA can be misused. It highlights the importance of being cautious while browsing unknown websites. A simple rule is to never send an SMS just to prove you are human online.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news










