A new cyber espionage campaign has been discovered where a Chinese-linked hacking group is targeting Mongolia using a different approach. Instead of only using traditional hacking tools, the attackers are abusing trusted cloud platforms. This makes their activity look normal and harder to detect. Since these services are commonly used in daily work, security systems may not easily flag them. This shows how modern cyber threats are becoming more advanced and subtle.

The group behind this campaign has been named GopherWhisper by cybersecurity researchers. Although the campaign is being reported recently, evidence shows that it has been active since at least November 2023. This means the attackers were operating quietly for a long time before being discovered. Their main objective appears to be cyber espionage rather than financial gain. This pattern is often seen in state-linked hacking groups.
The primary target of this operation is the government sector in Mongolia. Researchers found that at least 12 systems within one government organization were infected. There are also signs that more systems across different departments may have been affected. This suggests that the attack is part of a larger and well-planned campaign. It is not just a one-time incident but a targeted effort.
One important feature of this campaign is the use of multiple backdoor programs. The group has developed several tools such as LaxGopher, CompactGopher, and RatGopher. Each tool works in a slightly different way but serves the same purpose. These backdoors help the attackers maintain access to infected systems. Using multiple tools gives them flexibility if one method gets detected.
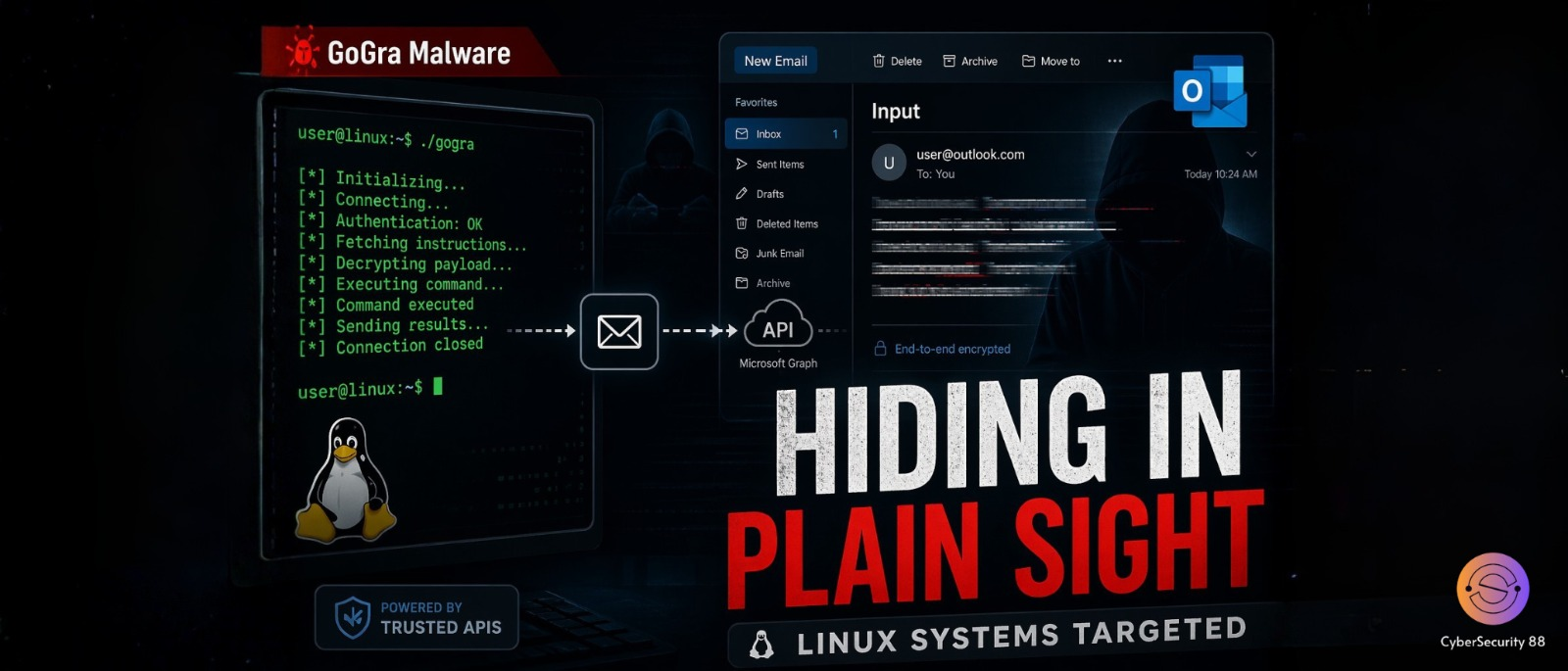
What makes this attack unique is how these tools communicate with the attackers. Instead of using traditional command-and-control servers, they rely on cloud-based services. These include platforms like Microsoft Outlook, Slack, Discord, and file-sharing services. Since these platforms are trusted and widely used, the malicious activity blends in easily. This makes it much harder to detect the attack.
Each backdoor uses a different cloud platform for communication. For example, one tool may operate through Slack, while another uses Discord. Some tools even use email drafts in Outlook to exchange commands and data. There is also a tool designed to steal files using cloud storage services. This multi-platform approach makes the attack more resilient. It also makes blocking all channels very difficult.
Researchers have also observed that the group may not be highly advanced compared to other APT groups. However, they compensate for this by using multiple tools and adapting quickly. Their strategy focuses on flexibility rather than complexity. They continue to experiment and improve their techniques over time. This makes them unpredictable and still a serious threat.
In conclusion, this campaign highlights a growing trend in cybersecurity. Attackers are now using trusted cloud services to hide their operations. This makes detection more challenging for security teams. The GopherWhisper case shows the importance of monitoring even normal-looking activities. As threats continue to evolve, organizations must strengthen their defenses and stay alert.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news