A new malware called GoGra has recently been discovered, and it mainly targets Linux systems. It is written in the Go programming language and is designed to stay hidden for a long time. What makes it different from normal malware is the way it communicates with attackers. Instead of using suspicious servers, it uses trusted cloud services to avoid detection. Security researchers have confirmed that this malware has already been used in real-world attacks.

GoGra works as a backdoor, which means once it enters a system, attackers can control that system remotely. The exact entry method is still not clearly known at this point. However, after entering, it quietly connects to Microsoft services to receive commands. Since these services are commonly used, the activity appears normal to security systems. This makes it very difficult to detect the malware in its early stages.
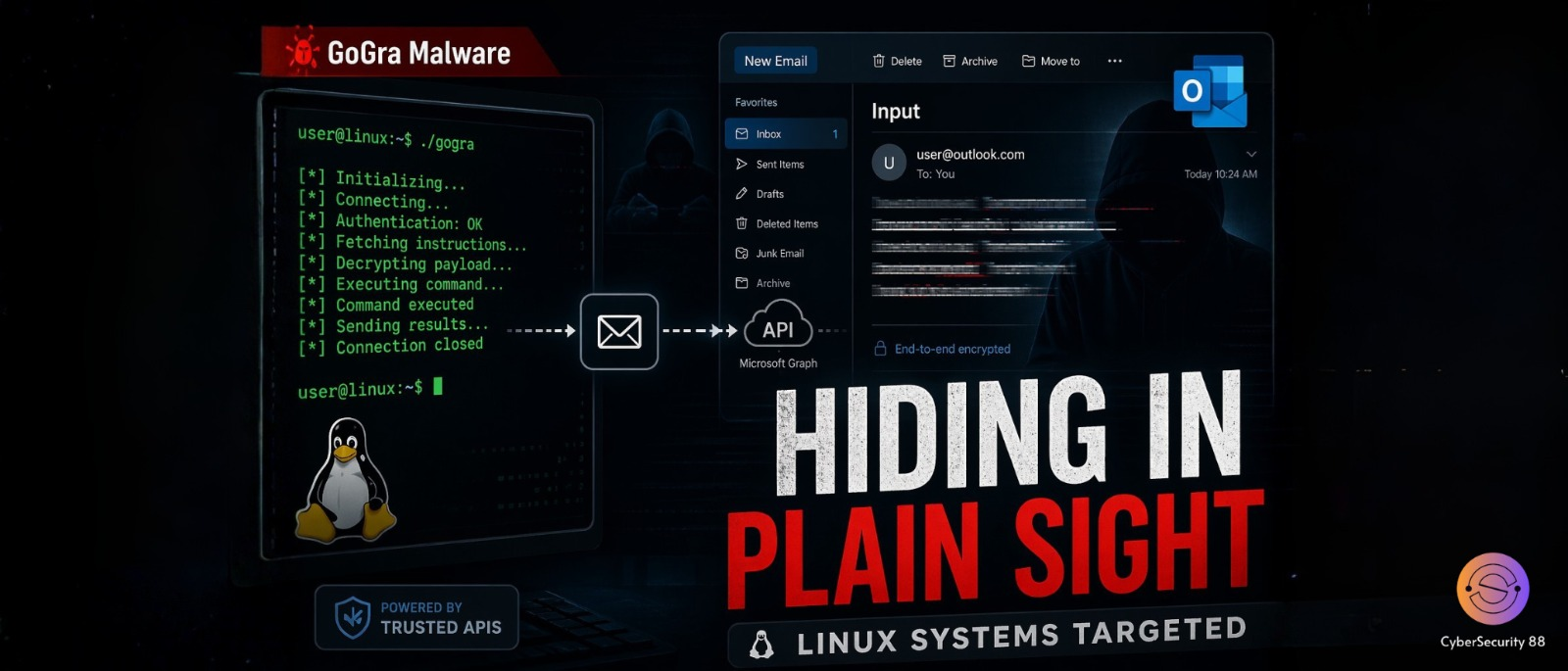
The most important feature of GoGra is its use of the Microsoft Graph API for communication. This API is normally used by apps to interact with services like Outlook and OneDrive. In this case, attackers misuse it to send commands to infected systems. The malware reads emails from an attacker-controlled account to get instructions. This allows it to blend in with regular cloud activity without raising suspicion.
The communication process is carefully designed to stay hidden and avoid detection. Commands are sent through emails with specific subject lines such as “Input.” The malware checks these emails and decrypts the content using AES-256 encryption. After that, it executes the commands directly on the infected system. Once the task is completed, it sends results back using emails with the subject “Output.”
Experts believe that GoGra may be linked to a nation-state level threat group. It shares similarities with earlier malware like Graphon, which used similar techniques. Such attacks are usually highly targeted and not random in nature. This suggests that the attackers carefully plan their operations before executing them. It also increases the seriousness of the threat for targeted organizations.
This malware highlights a growing trend in modern cyberattacks across the world. Attackers are now using trusted platforms like Microsoft cloud services instead of their own servers. Since these platforms are widely used, blocking them is not practical for organizations. This allows attackers to hide their activity within normal network traffic. As a result, detection becomes much more challenging for security teams.
Another important point is that this method is cost-effective for attackers. They do not need to build or maintain their own infrastructure for communication. Cloud services provide everything they need in a scalable way. At the same time, this creates major challenges for defenders trying to detect threats. Security teams must work harder to identify unusual behavior within normal traffic.
To stay protected, experts recommend strong security practices and monitoring. Organizations should keep an eye on unusual API activity, especially related to Microsoft Graph. They should also monitor suspicious email patterns and account usage. Limiting access privileges and performing regular audits can reduce risk significantly. Overall, GoGra shows how modern malware is becoming more advanced and difficult to detect.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news