Search for topics
Trending Searches
Featured Articles

ScarCruft Exploits Gaming Platform to Deploy BirdCall Malware on Android and Windows
May 05, 2026
A recent cybersecurity report has revealed a serious attack carried out by a North Korea-linked h...
Read More >
CloudZ Malware Exploits Microsoft Phone Link to Steal SMS and OTPs from Windows PCs
May 05, 2026
A new cybersecurity threat called CloudZ malware has recently come into focus, and it’s quite c...
Read More >
Critical MOVEit Automation Flaw Allows Authentication Bypass, Warns Progress Software
May 04, 2026
A serious cybersecurity issue has recently been identified in MOVEit Automation, a file transfer ...
Read More >
Silver Fox Targets India and Russia with ABCDoor Malware Using Tax-Themed Phishing Emails
May 04, 2026
A new cyberattack campaign has recently come into focus where a China-linked threat group called ...
Read More >
Mini Shai-Hulud Attack Targets SAP npm Packages, Exposes Developer Credentials
May 01, 2026
A new cyberattack called “Mini Shai-Hulud” has been discovered and is linked to a group known...
Read More >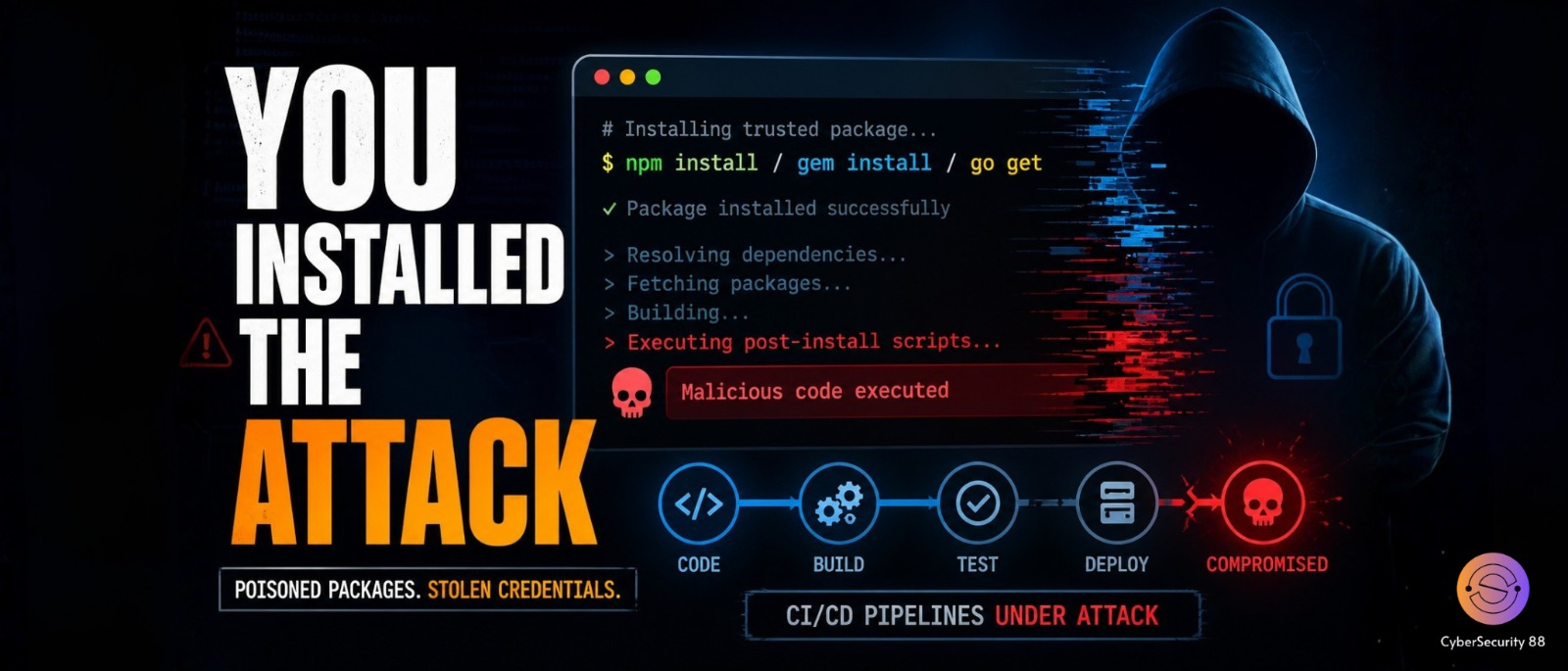
Poisoned Ruby Gems and Go Modules Target CI/CD Pipelines for Credential Theft
May 01, 2026
A new cybersecurity threat has been discovered where attackers are using fake open-source package...
Read More >
Critical “Copy Fail” Linux Vulnerability Allows Root Access Across Major Distributions
April 30, 2026
A new vulnerability called “Copy Fail” has been discovered in Linux systems and it is being t...
Read More >

