Cybersecurity researchers at Trend Micro have uncovered a sophisticated campaign by North Korea-linked threat actor group Void Dokkaebi, which used a fictitious company called BlockNovas to lure job seekers into downloading malware disguised as part of an interview process.
This campaign, run across platforms like LinkedIn, Upwork, and Freelancer, has already affected hundreds of applicants in Ukraine, Germany, United States and Ecuador.
BlockNovas positioned itself as a blockchain technology startup, with a sleek website, professional social media presence, and convincing online personas, including fake executives like a Chief Technology Officer with hundreds of LinkedIn followers. In reality, however, the company was a front for delivering malicious software including Beavertail, FrostyFerret (macOS), GolangGhost (Windows), and Invisible Ferret.
Malware Delivered as a Camera Fix
Job applicants were enticed with high-paying remote roles in the Web3 and blockchain space. what appeared to be a camera software update to proceed—this was, in fact, malware. Researchers from Trend Micro tested the interview workflow and confirmed the presence of malware installations disguised as legitimate software.

The malicious software enabled attackers to steal cryptocurrency and potentially exfiltrate sensitive data. In some cases, once initial access was gained, the infected system appeared to be handed off to a secondary team focused on espionage rather than financial theft. Targets extended beyond tech professionals to include individuals working in the energy sector.
A Russian Nexus in a North Korean Operation
Deeper investigation by Trend Micro revealed that many of the anonymization layers used by BlockNovas-connected servers traced back to IP ranges in Russia—specifically towns like Khasan and Khabarovsk. These IP ranges have been active since 2017 and a notable surge in their activity was observed. Researchers hypothesize that major North Korean cyber operations may be routed through these Russian locations.
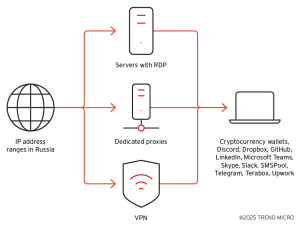
Supporting this theory, the same Russian IP ranges were used to manage Beavertail command-and-control (C&C) servers via VPNs, proxies, and RDP (Remote Desktop Protocol) sessions. These servers connected frequently to communication platforms like Discord, Mattermost, Skype, Microsoft Teams, Slack, and Telegram—as well as job recruitment websites, cryptocurrency exchanges, and development platforms such as GitHub and Visual Studio Code.
One of the tools found on BlockNovas’ mail server was Hashtopolis, a password cracking utility, suggesting the actors were prepared for deeper system penetration.
Seized and Shut Down
BlockNovas.com was registered on July 16, 2024, and listed a bogus South Carolina address that turned out to be an empty lot. As of April 23, 2025, the FBI and the U.S. Department of Justice have seized the domain and taken down the associated infrastructure.
Security researchers found that BlockNovas’ GitLab repository hosted known Beavertail samples, both in public and private repositories. A “status” page hosted by BlockNovas also listed several affiliated malware domains.
Mitigation
This campaign highlights a growing trend of exploiting popular platforms like Upwork and LinkedIn to spread malware. IT professionals looking for a job should be vigilant during remote interviews. Any request to download or execute software should be treated with suspicion and only run within a secure, isolated virtual environment. After the task, the environment should be destroyed to prevent data leaks.
Follow cybersecurity88 on X and Linkedin for the latest cybersecurity news
Source:hxxps[://]www[.]trendmicro[.]com/en_us/research/25/d/russian-infrastructure-north-korean-cybercrime.html








