Socket’s Threat Research Team has identified a coordinated and ongoing malicious campaign targeting the npm ecosystem, involving at least 60 packages designed to quietly exfiltrate sensitive system information to a threat actor-controlled Discord webhook.

What Does it Do?
The malicious packages published under three separate npm accounts deploy post-install scripts that activate during npm install commands. These scripts harvest a range of system data, including hostnames, internal and external IP addresses, DNS server configurations, user directory paths, and other identifiers. The collected data is transmitted to a Discord endpoint operated by the attacker.

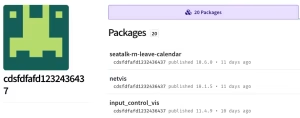

Each of the three npm accounts — bbbb335656, cdsfdfafd1232436437, and sdsds656565 has published exactly 20 malicious packages. Examples include seatable, datamart, and seamless-sppmy, each embedding identical host-fingerprinting code. The associated registration emails share a naming convention that further ties the campaign together.
An in-depth analysis by Socket revealed the script’s sole purpose is to fingerprint host machines, connecting private developer environments with their public-facing infrastructure. This type of intelligence is particularly dangerous on continuous-integration servers, where leaked details like internal registry URLs and build paths could streamline future attacks.
Impact
The campaign appears methodical and persistent. The first of these packages was uploaded eleven days ago, with the most recent surfacing just hours before this report, indicating that the operation is still active. The malware is designed to function on Windows, macOS, and Linux systems, and includes basic sandbox-evasion techniques, suggesting the actor is deliberately avoiding detection by researchers and automated analysis tools.
To date, the packages have amassed over 3,000 downloads, providing the attacker with a growing footprint across both individual developer environments and enterprise CI/CD pipelines. This reconnaissance enables a detailed mapping of internal network infrastructure for potential follow-on intrusions or supply chain attacks.
Despite the severity of the findings, all 60 packages remain live on the npm registry at the time of writing. Socket has formally petitioned for their removal and the suspension of the associated accounts, warning that the attacker could easily replicate the campaign with new accounts, packages, and exfiltration endpoints.
Conclusion
With npm lacking guardrails around post-install hooks, researchers warn that this quiet style of reconnaissance could inspire similar campaigns. Socket recommends that developers and organizations adopt more robust security measures, including dependency-scanning tools that flag suspicious patterns, such as post-install scripts and hardcoded URLs.
Tools such as the free Socket GitHub app, CLI, and browser extension can aid defenders by highlighting risky behavior in pull requests, package installations, and during online browsing of npm packages.
Source: hxxps[://]socket[.]dev/blog/60-malicious-npm-packages-leak-network-and-host-data
Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news







