Google’s Threat Intelligence Group (GTIG) has discovered a new malware called LOSTKEYS, attributed to the Russian government-backed hacking group COLDRIVER also known as UNC4057, Star Blizzard, and Callisto. LOSTKEYS is capable of exfiltrating sensitive files from specifically targeted directories and file types. It also transmits system details and a list of running processes back to its operators. GTIG observed the malware in campaigns conducted in January, March, and April 2025, signaling a notable evolution in COLDRIVER’s operational toolkit.
Targets of COLDRIVER’s Campaigns
The COLDRIVER threat group continues to focus its efforts on individuals and organizations aligned with Western interests and Ukrainian affairs. Their operations demonstrate a clear strategic intent to gather intelligence that could benefit Russian geopolitical objectives. Key targets identified in recent campaigns include:
- NATO governments
- Non-governmental organizations (NGOs)
- Former intelligence and diplomatic officers
- High-profile individuals
- Current and former advisors to Western governments and military institutions
- Journalists and ThinkTanks
- Individuals related to their Ukraine war
- UK-based officials and NGOs, some of whom were victims in hack-and-leak operations
LOSTKEYS Malware
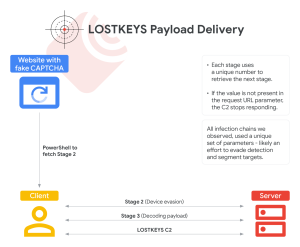
The LOSTKEYS infection chain begins with a malicious website displaying a fake CAPTCHA. Upon clicking through, users are prompted to paste and run a PowerShell command manually—a deceptive tactic known as “ClickFix.” This command initiates the first stage of malware delivery, fetching additional stages from the IP address 165.227.148[.]68.

In the second stage, the malware calculates the MD5 hash of the device’s display resolution to determine whether it is running in a virtual environment, a common method used by researchers and defenders. If the resolution matches any of three hard-coded hashes, the malware halts execution. Otherwise, it proceeds to the third stage, which again is pulled from the same server, and requires unique identifiers to access.
Stage three involves a Base64-encoded PowerShell script that downloads two additional files: a Visual Basic Script (VBS) decoder and an encoded payload. Using two unique decryption keys one in the decoder and one embedded in the script—the malware decrypts the final VBS payload: LOSTKEYS.
This final component is designed to steal files and system information. Like SPICA, LOSTKEYS appears to be deployed only against high-value targets where gaining access to stored documents is of strategic interest.
The Bottom Line
GTIG warns that socially engineered malware delivery methods like ClickFix are gaining traction across multiple threat groups, both state-sponsored and financially motivated. Organizations are urged to adopt stringent security policies, restrict script execution, and train personnel to recognize suspicious prompts to run code manually.
Indicators of Compromise (IOCs) and technical details related to LOSTKEYS are shared in GTIG’s blog.
Source: hxxps[://]cloud[.]google[.]com/blog/topics/threat-intelligence/coldriver-steal-documents-western-targets-ngos
Follow Cybersecurity88 on X and Linkedin for the latest cybersecurity news








