On May 5 at 16:00 GMT, cybersecurity firm Aikido’s automated malware analysis pipeline detected a serious supply chain compromise in the npm package rand-user-agent@1.0.110. The package, which averages approximately 45,000 weekly downloads, was found to contain malicious code designed to carry out remote access and data exfiltration.
The rand-user-agent package, maintained by WebScrapingAPI, is widely used for generating randomized real user-agent strings based on usage frequency. However, recent activity revealed a disturbing development: a suspicious release of version 1.0.110 that contained obfuscated malicious code.
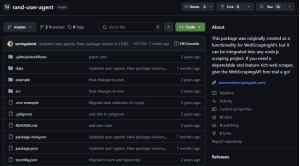
Upon investigation, Aikido found discrepancies between the package’s official GitHub repository and its npm release history. The last legitimate GitHub commit was made seven months ago, marking version 2.0.82. Since then, multiple versions have been published to npm and all of which contain signs of compromise, confirming a targeted supply chain attack.
Malicious Payload Details
The core of the attack is a Remote Access Trojan (RAT), cleverly hide it through several layers of obfuscation. Once active, the script establishes a covert communication channel with a command-and-control (C2) server using the socket.io-client module, and exfiltrates sensitive files to an alternate endpoint using axios.
To further evade detection, the malware installs its dependencies into a hidden .node_modules folder located in the user’s home directory.
C2 Infrastructure
Socket Communication: http://85.239.62[.]36:3306
File Upload Endpoint: http://85.239.62[.]36:27017/u/f
Upon connecting, the infected client transmits identifying details including hostname, username, operating system, and process ID.
Notably, the RAT includes a Windows-specific PATH hijacking mechanism. It injects a custom directory into the beginning of the PATH environment variable. This allows the malware to hijack execution of common Python-related commands like python or pip, exploiting environments where Python is routinely expected to be present.
By manipulating system behaviour in this subtle yet powerful way, the attacker ensures prolonged persistence and stealthy execution — a hallmark of sophisticated supply chain threats.
IOC
-
-
- 2.0.83
- 2.0.84
- 1.0.110
- Socket Communication
http://85.239.62[.]36:3306
-
-
- File Upload Endpoint code>http://85.239.62[.]36:27017/u/f
The Bottom Line
This incident underscores the increasing threat of supply chain attacks in open-source ecosystems. Developers and users are urged to:
- Review recent versions of rand-user-agent and revert to trusted releases.
- Scan systems for unauthorized network connections or unexpected .node_modules directories.
- Monitor environment variables, particularly PATH, for suspicious modifications.
WebScrapingAPI has yet to release an official statement regarding the compromise.
Source: hxxps[://]www[.]aikido[.]dev/blog/catching-a-rat-remote-access-trojian-rand-user-agent-supply-chain-compromise
Follow Cybersecurity88 on X and Linkedin for the latest cybersecurity news







