In a new wave of cyberattacks, Russia-linked threat actors are exploiting legitimate Auth 2.0 authentication processes to compromise Microsoft 365 accounts belonging to individuals affiliated with Ukraine and human rights organizations, according to a report by cybersecurity firm Volexity.
The adversaries—tracked by Volexity as UTA0352 and UTA0355—have been conducting the operation since early March, shortly after a similar campaign was exposed by Volexity and Microsoft in February. Both campaigns use sophisticated phishing tactics that abuse Microsoft’s Device Code Authentication flow to steal credentials and maintain persistent access.
Sophisticated Social Engineering to Exploit OAuth 2.0
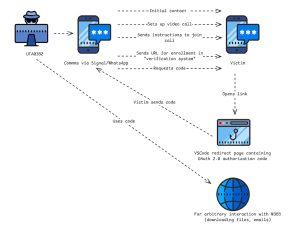
According to the report, the attackers initiate contact via popular messaging platforms WhatsApp and Signal, posing as European officials or Ukrainian diplomats. The initial message was an invitation to a confidential video meeting on Ukraine-related matters.
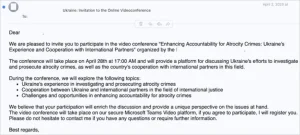
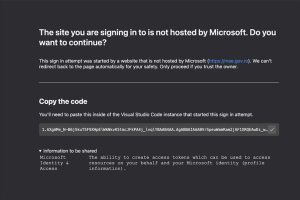
Once trust is established, victims are directed to malicious OAuth phishing URLs, sometimes embedded in PDF documents, which mimic Microsoft login workflows. These links, when clicked, redirect users to a Visual Studio Code-branded interface hosted at insiders.vscode.dev. Here, the victim is asked to authenticate, supposedly to join the video meeting.
The attackers use this fake interface to collect OAuth authorization codes, under the pretense that they are required to join the call. The codes are then used to grant the attacker access to the victim’s Microsoft 365 account.
Evolving tactics
UTA0355, active in April, used a variation of this technique, launching attacks from a compromised Ukrainian government email account. After gaining the OAuth code, the attacker registered a new device to the victim’s Microsoft Entra ID (formerly Azure Active Directory), and then manipulated the victim into approving a two-factor authentication (2FA) request.
In one instance, the attacker falsely claimed that the 2FA code was needed to access a SharePoint instance related to the purported meeting. This step allowed the attacker to secure a token with extended access to the victim’s emails and resources.
The stolen authorization code is valid for 60 days and can be used to retrieve an access token for all services the user normally has access to.
Recommendations and Mitigations
Volexity is urging organizations to:
- Set alerts for logins using the Visual Studio Code client ID
- Block access to the domains
insiders.vscode.devandvscode-redirect.azurewebsites.net</li> - Enforce conditional access policies to allow logins only from approved devices
It’s worth noting that just last month, CERT-UA reported the use of Signal to distribute malware by sharing documents related to drones. We also previously highlighted a sophisticated phishing campaign in which cybercriminals deployed malicious Microsoft OAuth applications disguised as legitimate Adobe and DocuSign apps to steal Microsoft 365 credentials and spread malware.
Follow cybersecurity88 on X and Linkedin for the latest cybersecurity news
Source:hxxps[://]www[.]volexity[.]com/blog/2025/04/22/phishing-for-codes-russian-threat-actors-target-microsoft-365-oauth-workflows/