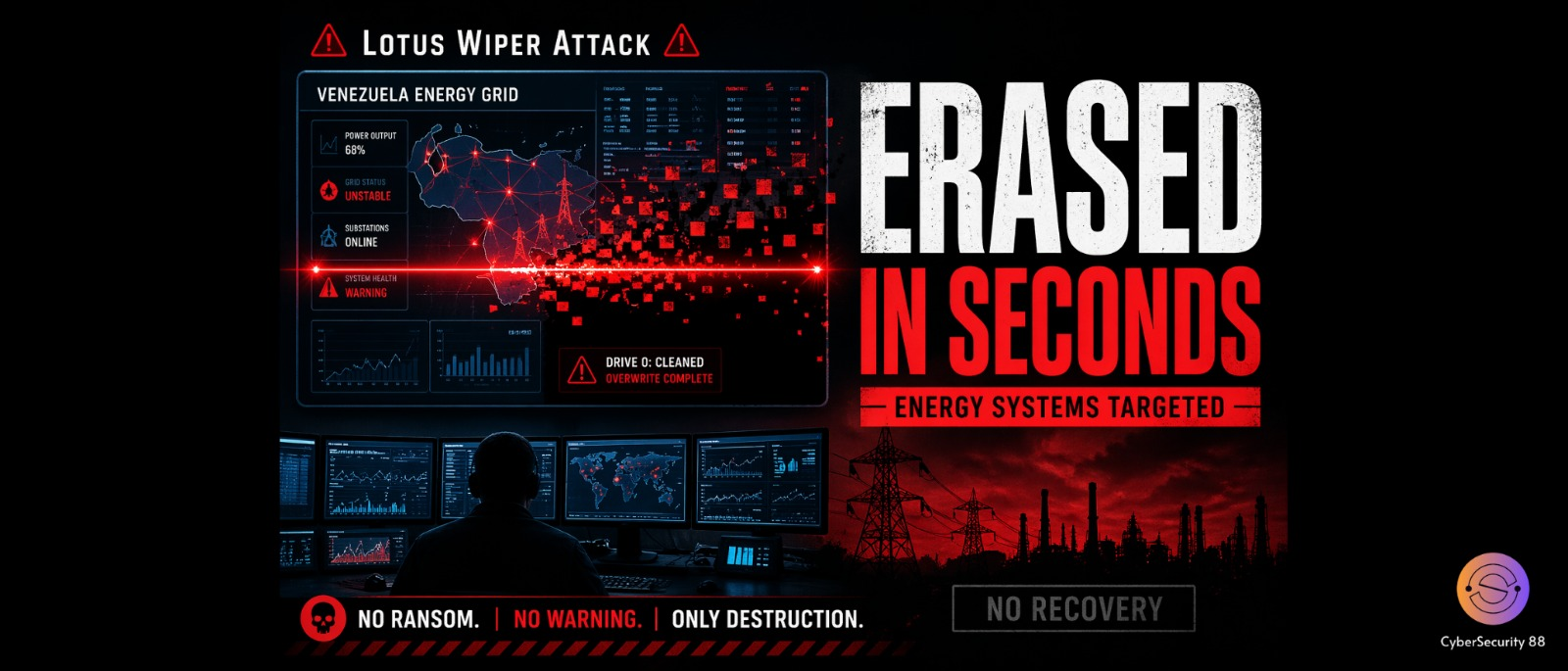
A new cyber threat called Lotus Wiper has recently been identified in attacks targeting Venezuela’s energy and utilities sector. This is not a typical cyberattack that focuses on stealing money or sensitive information from organizations. Instead, it is designed to completely destroy systems and make them unusable for operations. Security researchers, including teams from Kaspersky, observed this campaign and confirmed its activity timeline. The attack was mainly active between late 2025 and early 2026, focusing on critical infrastructure.

What makes Lotus Wiper especially dangerous is its nature as a destructive malware. It belongs to a category known as wiper malware, which focuses on permanent data deletion. Once it infects a system, it starts overwriting hard drives with useless data. It deletes files across all storage volumes and removes recovery options completely. This ensures that the affected system cannot be restored easily or sometimes not at all.
Another serious aspect of this malware is its ability to remove traces after execution. It clears logs and system records, making investigation very difficult for security teams. This means organizations may not even fully understand how the attack happened. The damage caused is not only technical but also operational for the organization. In most cases, data recovery becomes nearly impossible after the attack. As a result, systems become permanently unusable.
The attack process itself is carefully planned and executed in multiple stages. In the first stage, attackers use batch scripts to prepare the system environment. These scripts disable security protections and interfere with normal system operations. They also help attackers coordinate actions across multiple systems in the network. This stage clearly indicates that attackers already had deep access to the system. It was not a random or sudden attack but a planned one.
In the next stage, the malware uses a trigger-based mechanism to move forward. A script checks certain system conditions before continuing execution. A hidden file acts as a signal that activates the next step of the attack. Once triggered, another script prepares the system for complete destruction. During this phase, users are logged out and accounts are disabled forcefully. Network connections are also shut down to isolate the system.
After preparation, the final payload of Lotus Wiper is executed on the system. At this stage, the malware begins wiping all data from the system completely. It deletes files, overwrites storage, and renames data to hide traces. Multiple wiping processes are executed to ensure no data remains recoverable. This makes the system fully unusable and beyond repair. Unlike ransomware, there is no demand for money or recovery option.
The main targets of this campaign were organizations in Venezuela’s energy sector. The intention behind the attack was not financial gain but complete disruption. Researchers believe attackers spent a long time inside the network before launching the attack. They likely studied the system and planned each step carefully in advance. The identity of the attackers is still unknown at this point. This makes the attack even more concerning from a security perspective.
This incident highlights a shift in modern cyberattack strategies across the world. Instead of focusing only on financial gain, attackers are now aiming for destruction. Critical sectors like energy and utilities are becoming major targets for such attacks. To prevent such incidents, organizations must monitor unusual activities and restrict access controls. Maintaining secure backups and tracking system behavior is also very important. Overall, Lotus Wiper shows how dangerous and destructive cyber threats have become today.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news