A new cyber-espionage campaign has recently been discovered targeting government systems in Mongolia. Security researchers identified a group called GopherWhisper, which is believed to be linked to China. This group managed to infect at least 12 government systems using advanced malware. The malware used in this attack was written in the Go programming language. This language is increasingly used by attackers because it is fast, flexible, and works across different systems.
The investigation began when unusual activity was detected inside a Mongolian government network. Researchers closely analyzed the behavior and found that it was not a simple or random attack. Instead, it was a carefully planned operation designed to stay hidden for a long time. During the investigation, a new backdoor named LaxGopher was discovered. This backdoor allowed attackers to quietly monitor and control infected systems. The overall goal of the attack was long-term cyber-espionage rather than immediate damage.
The attackers mainly relied on Go-based malware to carry out their operations. This type of malware allows them to run their tools smoothly on different platforms without much difficulty. Along with LaxGopher, they used other tools such as JabGopher to deliver malicious payloads. These tools help in spreading the infection deeper into the network. Once installed, the malware gives attackers the ability to execute commands remotely. It also allows them to upload, download, and manage files without being detected easily.
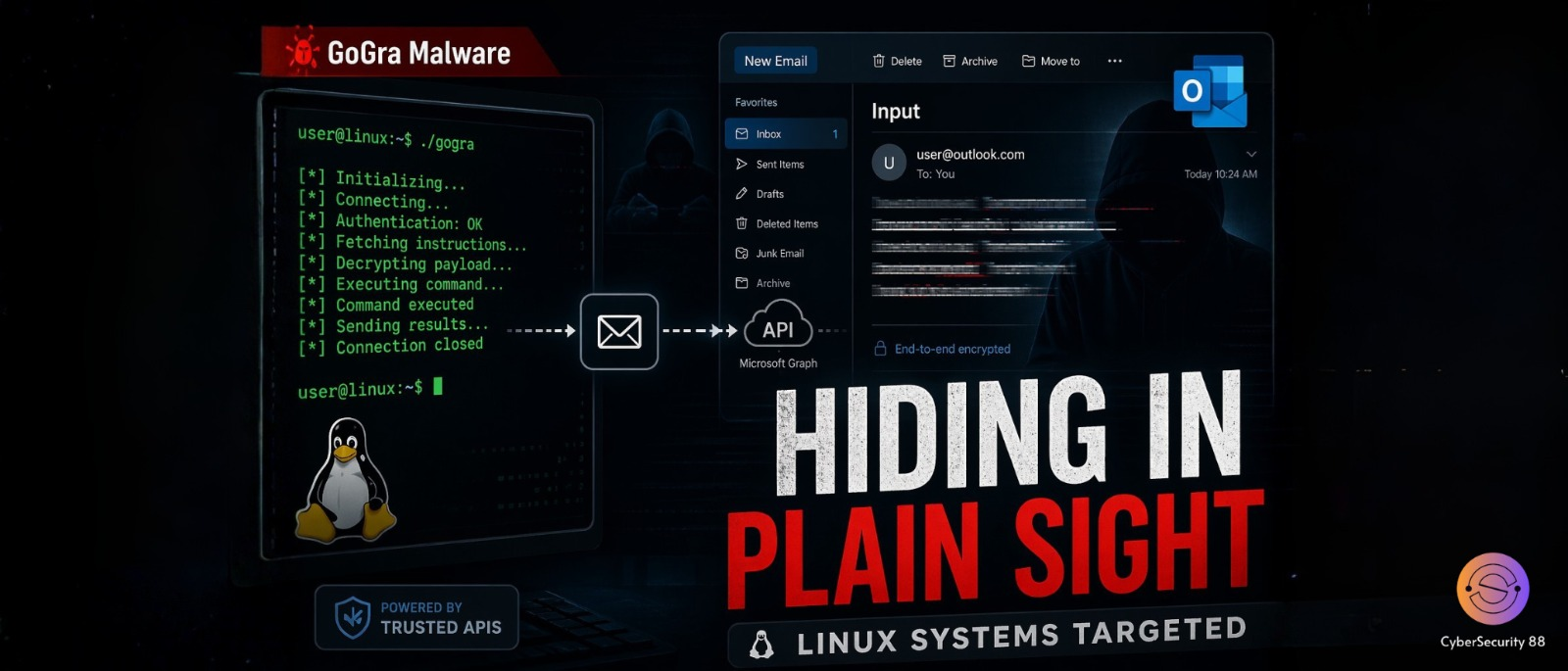
One of the most dangerous aspects of this attack is the use of trusted platforms for communication. Instead of using suspicious servers, the attackers used common services like Slack, Discord, and Microsoft Outlook. Some malware variants communicated through Slack channels to receive instructions. Others used Discord servers to execute commands remotely. In certain cases, Outlook draft emails were used to pass hidden messages. This method helps attackers hide their activities within normal network traffic and avoid detection.
The attackers deployed a complete toolkit of malware to maintain control over infected systems. LaxGopher acted as the main backdoor and handled communication through Slack. Another tool, RatGopher, used Discord to receive commands and control infected machines. CompactGopher was responsible for collecting and compressing sensitive data. There was also a C++ based backdoor called SSLORDoor for deeper system access. Another tool named BoxOfFriends used Microsoft Graph API for stealthy communication.
So far, around 12 systems within Mongolian government institutions have been confirmed as infected. However, researchers believe that the actual number of affected systems may be higher. Some attacker communication logs suggest that more systems were targeted during the campaign. This indicates that the attack may have been larger than initially observed. It also raises concerns that some infections may still remain undetected. The full scale of the operation is still being investigated.
There are several indicators that suggest a link between this attack and China. The timing of the activity matches standard working hours in China, typically between 8 AM and 5 PM. This pattern is often seen in state-linked cyber operations. In addition, some system configurations and metadata were found to be set in the Chinese language. These technical clues strengthen the suspicion of Chinese involvement. However, exact attribution in cyberattacks is always complex and requires careful analysis.
The exact method used by attackers to initially access the systems is still unknown. Researchers have not yet identified how the attackers entered the network for the first time. Despite this, once they gained access, they quickly deployed multiple tools to expand their control. The attack highlights how cyber threats are becoming more advanced and harder to detect. It also shows how trusted platforms can be misused for malicious purposes. Overall, this incident raises serious concerns about the security of critical government systems.
Stay alert, and keep your security measures updated!
Source: Follow cybersecurity88 on X and LinkedIn for the latest cybersecurity news