The notorious Phishing-as-a-service (PhaaS) platform Tycoon2FA kit has introduced several new evasion techniques to bypass EDR solutions and detection mechanism. Tycoon 2FA kit uses custom CAPTCHA rendered using HTML5 canvas, Unicode characters in obfuscated JavaScript, and anti-debugging scripts to bypass detection mechanisms and EDR.
Technical analysis
Tycoon2FA was initially by Sekoia researchers in October 2023. Now after two years it came back with a several improvements that improve its persistence and longevity in systems. One of the standout features in the latest campaign is the use of invisible Unicode characters in obfuscated JavaScript code.
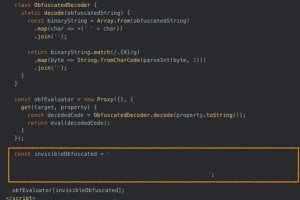
By using characters like Halfwidth Hangul Filler (\uFFA0) and Hangul Filler (\u3164) to represent binary data, threat actors are able to encode and decode malicious scripts that are invisible to detect and difficult for static analysis tools to detect.
Previously reliant on third-party solutions like Cloudflare Turnstile, Tycoon 2FA has shifted to a fully custom CAPTCHA rendered via HTML5 canvas. This change reduces its detectability by removing telltale signs of third-party elements. The new CAPTCHA introduces randomized characters, distortion, and visual noise, closely mimicking legitimate authentication workflows.
When users complete the CAPTCHA successfully, the phishing site forwards form data to attacker-controlled infrastructure. In cases of errors or failed responses, a base64-encoded decoy page is injected to avoid suspicion.
Fighting Back Against Researchers
The Tycoon 2FA kit also includes a battery of anti-debugging scripts aimed at frustrating analysts and automated tools. These scripts:
- Detect browser frameworks like PhantomJS and Burp Suite.
- Block developer tools access via keyboard shortcuts (e.g., F12, Ctrl+Shift+I).
- Disable right-click functionality to prevent inspection.
- Use timing-based checks to detect if execution is paused.
- Redirect users to benign websites like rakuten.com if analysis is suspected.
Conclusion
The rise of advanced phishing kits like Tycoon 2FA and LucidPhaaS shows an increase in the availability and sophistication of Phishing-as-a-Service offerings on underground marketplaces. Not only are these kits becoming more evasive and harder to detect, but some are also believed to be backed or used by nation-state actors.

To help detect this specific threat, researchers at Trustwave have released a YARA rule targeting Tycoon 2FA’s unique characteristics. However, detection alone is not enough. As phishing attacks continue to evolve, it’s more important than ever for organizations to invest in employee security awareness training and adopt more advanced security solutions, including threat intelligence platforms, behavioral detection, and endpoint protection tools.
Follow us on X and Linkedin for the latest cybersecurity news
Source:hxxps[://]www[.]trustwave[.]com/en-us/resources/blogs/spiderlabs-blog/tycoon2fa-new-evasion-technique-for-2025/







